
26 Best Report Writing Topics For Students
Stumped while brainstorming report writing topics ? We’ve got your back. Take a look at our list of interesting-to-research report topics for students .
Completing a research report for a high school or college English class can be a great way to show off your smarts or interest in a topic, but figuring out where to start can be challenging. Choosing a topic that interests you is an essential part of getting started. The more curious you are about your chosen topic, the more interested you’ll be in the research process.
Choose from our list of sample essay topics below to show off your writing skills — we have options that work for several types of report writing formats. If you’re still stuck picking your next essay topic, check out our round-up of essay topics about education .
1. Technology’s Effect on Society
2. gun control in america, 3. anxiety and social media, 4. present-day slavery, 5. should assisted suicide be legal, 6. the draft’s history in america, 7. no child left behind: did it work, 8. the bp oil spill: 12 years later, 9. parental leave around the world, 10. the insanity plea, 12. trans rights: at what age should a person be legally allowed to transition, 13. should school uniforms be mandatory, 14. compare the uk and us education systems, 15. discuss the pros and cons of violent tv shows for teens, 16. analyze how peer pressure impacts teenagers, 17. does music have healing powers, 18. analyze the causes of wildfires, 19. discuss the impact of global warming on the environment, 20. how does single parenting impact the upbringing of a child, 21. what are the social impacts of the covid-19 pandemic, 22. the effects of urbanization on wildlife, 23. mental health impact of social media on teens, 24. sustainable farming practices and food security, 25. the rise of e-learning, 26. impact of plastic waste on marine life.

Technology makes our lives easier in many ways, but today’s tech-heavy society can also have detrimental effects. Some people find they must always be reachable due to constant access through email and cell phones, while others appreciate instant access to the people closest to them.
In a research report on how technology affects today’s society, you can focus on both sides, touching on how technology makes life easier and affects relationships and work-life balance. Discuss how technology has positively affected medical care and how the overuse of technology has contributed to health issues (including an increasingly sedentary lifestyle). Be sure to back up your points with background information based on research.
Gun control in the United States is a controversial topic. This type of academic report can either be written as a report that presents both sides of a story or as a persuasive report that argues one side. People who are for gun control argue that access to guns increases the risk of violence in the United States. In contrast, people against gun control argue that guns aren’t responsible for deaths and violence.
While presenting this topic in a formal report, discuss the history of gun control in the United States. You may also want to consider comparing gun violence rates in the United States with gun violence in other countries and comparing gun control laws in the U.S. to gun control laws in other countries. Be sure to check your sources carefully when writing about gun control, and choose unbiased sources as often as possible.

It’s tough to avoid social media in today’s day and age. While many people find social media a valuable tool for keeping in touch with family and friends, others find apps like Facebook, Instagram, and TikTok to induce stress. Research shows that using social media can have an addictive effect, as scrolling through a social media app affects the brain’s levels of dopamine, a feel-good chemical.
The high associated with scrolling social media can become addictive. People may find themselves stuck in the downward spiral of scrolling for a dopamine hit, followed by comparing themselves to others, negatively affecting their self-esteem. In a paper on this topic, explore how cutting down on social media can relieve adolescent anxiety and explain how social media can also be used to boost self-esteem positively.
While many think of slavery as a thing of the past, the concept is still sadly alive today. This can be an emotional and tough topic to research and write about. Still, it can educate your readers about the harsh reality of present-day slavery, bringing attention to an issue that often goes ignored.
According to antislavery.org , nearly 50 million people live in modern-day slavery, and approximately 25% of modern-day enslaved people are children. There are many forms of modern-day slavery, including forced marriage, domestic servitude, forced labor, human trafficking, and descent-based slavery (when enslaved children are also forced to work as enslaved people). For your research report on present-day slavery, you may focus on one of these areas or explore the concept of modern-day slavery as a whole.
Many people who have experienced the death of a loved one have struggled to watch them suffer and have wished that there was something they could do to help them end their suffering. In some states in America, assisted suicide has become legal . This means that a person who is terminally ill can work with their medical treatment team to develop a plan to die on their own terms.
Some people are against assisted suicide and believe people should be unable to choose how and when they’ll die. In contrast, others feel that allowing people to choose their time of death following a diagnosis of a terminal illness allows them to pass away with dignity.
This report writing topic for students can work as an informational or persuasive essay. If you have strong feelings on the topic, be sure to present both sides of the argument and your personal opinion on your point of view. You’ll also want to be sure to touch on the history of assisted suicide in the United States and views on assisted suicide around the world, as the practice is common in many areas of the world.
The draft in the United States dictates that any male over the age of 18 can be called to military service in times of war. While some people believe that the draft is outdated and should be left behind , others believe that the draft still has a place in America.
This topic can work either as a research report or a persuasive essay. If you can, talking with a military veteran who began their service due to the draft can help bring realism to your report. You may also want to talk with people who left the country to avoid the draft.
While the draft currently can only bring men to military service, some people believe that women should also be able to be drafted. Discussing this aspect of the history of the draft in the United States can add an exciting aspect to your report.
No Child Left Behind was enacted by President George W. Bush and was in effect from 2002-2015. The law rewarded teachers and schools for having high-performing classrooms and penalized schools that did not perform up to par. While some people felt that the law was the right thing to keep schools accountable for student progress, others felt that it kept disadvantaged students at a disadvantage instead of providing teachers and schools with the support they needed to achieve.
While some schools rose to the challenges of No Child Left Behind, others struggled. In an essay on the topic, you’ll need to form your own opinion on whether NCLB was an effective law for education in the United States. You may want to interview educators and administrators working in schools during the No Child Left Behind era to get firsthand opinions on whether the laws were adequate.
Also known as the Deepwater Horizon oil spill , the BP oil spill occurred on April 20, 2021, and spilled more than 130 million gallons off the Gulf of Mexico near the New Othe Orleans, Louisiana coast. The effects of the BP oil spill are still being felt in the area more than a decade later.
You can go in several different directions while reporting on the effects of the BP oil spill. The animal and plant life in the area is still suffering from the spill’s effects. People in the area are also struggling, especially those who made a living fishing off the coast. Tourism in the area has also been affected, leaving many people in New Orleans struggling to make ends meet.
The length of your research paper will determine how in-depth you can go with the topic. If you’re writing a shorter research paper, it’s wise to choose one of the topics (how the spill has affected the area’s economy, wildlife, tourism, etc.). If you’re writing a longer research paper, split it into subheadings so you can fully delve into each facet of the topic.
Many parents in the United States struggle to make ends meet following the birth of a child due to the short time that companies are required to give parents after they welcome a baby into their home. While the United Nations recommends that mothers have at least four months to recover after giving birth, the United States has no federal requirement for parental leave .
While researching this issue, it’s key to explain the differences between how new parents are treated in the United States compared to other countries and how this treatment affects both the stress levels and job performance of new parents. You’ll want to be sure to look at both sides of the issue, also explaining how the lack of a federally mandated parental leave policy can affect companies.
In the United States, a person can be found not guilty of a crime because of insanity. This means that the person accused of a crime isn’t found innocent—the court has decided that they could not understand the severity of the crime. Some people argue that people should not be able to plead insanity after committing a crime, as the crime occurred whether they understood their actions or not. Others argue that the insanity defense is necessary to protect people who do not understand the consequences of their actions.
When writing a research paper on the insanity defense, it’s key to include examples from real-life legal cases, such as the Steven Steinberg case (1981) . Mr. Steinberg claimed he was sleepwalking and dreaming about a break-in to his home when he stabbed and killed his wife. Steinberg was found not guilty due to temporary insanity, as the jury decided he was not in his right mind when the crime occurred.

Transgender health has received a lot of attention in the news recently, and one of the most commonly debated topics in the transgender health medical community is at what age it makes sense for people who are transgender to begin taking hormones and undergo surgical procedures that allow their body to be in alignment with their gender identification.
According to AP News , “The World Professional Association for Transgender Health said hormones could be started at age 14, two years earlier than the group’s previous advice, and some surgeries are done at age 15 or 17, a year or so earlier than previous guidance.”
Digging into the current research on transgender health and gender dysphoria can help you determine your position on this issue. Be sure that the news sources you use are current, as research in this area constantly evolves. You’ll want to be sure you’re basing your opinion on the most up-to-date information from the medical community.
In most US schools, school uniforms aren’t mandatory; instead, the school enforces a dress code. Dress codes define the clothing the school board finds acceptable for students. The dress code can vary from school to school, but for the most part, it requires students to wear appropriate clothing that is not overly short, formal, or dressy. Some argue that allowing students to choose their clothing for school promotes individuality and confidence.
In other countries in the world, a school uniform is mandatory. The purpose of a school uniform is to eliminate any class issues where some children may be able to afford more fashionable clothes than others. A uniform ensures all students look the same and can be argued to promote a feeling of self-confidence and a sense of belonging amongst the students, removing the pressure on deciding what to wear and meeting peer expectations regarding fashion. Choose a side and argue your case in your report, citing sources and studies.
The education systems in the US and the UK have pros and cons. Some argue that the US approach allows for confidence building through more extracurricular activities, while others argue that the UK prioritizes subjects like Math and English from a younger age.
Study the differences in both education systems and choose which one you think is most beneficial to children. Does one education system set students up for success more than the other? Answer this in your own words to create an engaging argument.
Violent TV shows can have positive and negative impacts on teens worldwide. This report discusses the pros and cons of violent TV shows. Some pros include reinforcing morals and prior beliefs that violence is wrong and has negative consequences. However, some argue that violent TV shows can justify violence in the viewer’s mind.
In your report, analyze both sides of this argument and conclude by discussing your views. Include studies and data to support your arguments, looking at how violence can be perceived.
Peer pressure is one of the biggest challenges that teens face. Peer pressure can be severe, such as peer pressure to drink alcohol underage. However, it can also show up in milder ways, such as pressure to dress a certain way, listen to specific music, or follow the crowd.
In your report, discuss the impact of peer pressure on teenagers’ self-esteem and examine how individuality can be challenging to achieve. Discuss factors contributing to peer pressure, like social media, bullying, etc.
Music is argued to be a healing power for mental health, and physical conditions and can even help plants grow. Study this theory and use research data to determine whether this is true. In your report, describe how music can be healing, but also look at the limitations. To create a compelling report, source real data on how music has been used to heal a health condition and discuss how much it can help.

Wildfires are becoming increasingly common all around the world. In particular, the US sees a high number of wildfires every year. In August 2002, devastating wildfires across California left many people without homes.
This report, discusses the causes and effects of wildfires across the globe. Use this report as an opportunity to bring attention to the noticeable effects of global warming and include ways in which governments can work to reduce wildfires.
Global warming is becoming increasingly common, making it an essential topic for argumentative and analytical reports. In your report, discuss the climate changes and how they have impacted the environment.
For example, examine the glaciers and ice sheets shrinking, wildfires across the globe, and the overall temperature increase in countries worldwide. Use scientific data to back up your report, keeping it factual and informative.
Parenting is a common topic for research reports, examining how upbringing and circumstance can help or hinder a child’s development and well-being. Study the effects of living in a single-parent household versus a joint-parent household on the well-being and success of children. There are many arguments both for and against single parenting.
Some pros include that the child creates an excellent bond with the parent or the absent parent could negatively affect the child, so they shouldn’t be within the household. However, some cons can include the single parent becoming dependent on childcare. Discuss the effects of single parenting and look at both the positive and negative effects.
The Covid-19 pandemic has changed the world; with it, social issues have come into focus. Some of the most impactful social challenges of the pandemic are the increasing rates of anxiety and depression . In your report, research and identify the main social challenges that we have faced since the pandemic and discuss the steps that can be taken to recover. Use this report to discuss your own experiences and the challenges others have faced.
Explanation : Urbanization refers to the growth in population concentration in urban areas and its subsequent effects on the environment, economy, and society. One critical effect is on local wildlife, which can be displaced or endangered due to urban sprawl. Start by researching the local species affected by urban development in your region. They should gather data on species decline, habitat loss, or conservation efforts.
Consider visiting a local wildlife reserve or sanctuary. Interviewing experts or conservationists can provide firsthand insights works too.
The ubiquitous use of social media has led to various mental health concerns among teenagers, including issues related to self-esteem, peer pressure, and isolation. Analyze various scholarly articles and surveys highlighting the psychological effects of prolonged social media use. Contrast this with the potential positive aspects, like connectivity and information dissemination. Survey your school or community to gather primary data on the topic, this can make the report more relevant and localized.
Sustainable farming is a method of farming that incorporates practices that can sustain the farmer, resources, and the community at large. It often interlinks with food security, ensuring everyone can access sufficient, safe, nutritious food. Examine different sustainable farming methods, their benefits, and how they contribute to food security. Highlight challenges and propose potential solutions.
If possible, visit a local farm that employs sustainable practices. Real-world observations can add depth to your report.
E-learning refers to using electronic technologies to access educational content outside of a traditional classroom. With the rise of digital platforms and tools, e-learning has become more prevalent. Assess the advantages of e-learning, such as flexibility and accessibility, against its challenges, like lack of face-to-face interaction and potential distractions. Interview students or educators with firsthand experience with traditional and e-learning settings to provide a balanced view.
Plastic waste often ends up in our oceans, affecting marine life. From microscopic plankton to gigantic whales, marine organisms ingest or get entangled in plastic debris, leading to fatal consequences. Research the plastic journey from land to sea, the species most affected, and the overall ecological repercussions. Investigate potential solutions and conservation efforts.
Incorporate visuals, like photographs or infographics, to show the severity of ocean plastic pollution.
Looking for more advice about report writing topics? Check out our guide on how to write an argumentative essay .

Meet Rachael, the editor at Become a Writer Today. With years of experience in the field, she is passionate about language and dedicated to producing high-quality content that engages and informs readers. When she's not editing or writing, you can find her exploring the great outdoors, finding inspiration for her next project.
View all posts

Report Writing: Format, Topics, and Examples
Learn the essentials of report writing with this comprehensive guide. Explore the proper format, find inspiring topics, and discover real-world examples to enhance your report writing skills.
What is Report Writing?
A Report Writing is a written account that helps us to know about an event, situation, or occurrence in detail that has already taken place.
Report Writing is a narrative of Events described in an impartial approach. Rules and Format of Report Writing are necessary to know for English report writing. Examples of Report Writing help us in doing this easily.
The Power of Effective Report Writing
Report writing is a skill that transcends industries and disciplines, playing a vital role in conveying information, analyzing data, and making informed decisions.
Whether you are a student, a researcher, a business professional, or someone looking to improve your communication abilities, mastering the art of report writing is essential for success.
This article will provide you with insights into the format, topics, and real-world examples of report writing to help you become a proficient report writer.
Understanding the Format of a Report
A well-structured report not only facilitates easy comprehension but also leaves a lasting impact on the reader. Understanding the proper format is the foundation of creating an effective report. In crafting a comprehensive and impactful report, one must carefully consider and include the following crucial elements. :
1. Title Page
The title page should include the report’s title, the name of the author or organization, the date of submission, and any relevant affiliations.
2. Abstract or Executive Summary
The abstract or executive summary is a concise overview of the report’s main points, providing the reader with a snapshot of the entire report’s content.
3. Table of Contents
The table of contents outlines the report’s structure, listing the headings and subheadings with corresponding page numbers.
4. Introduction
The introduction sets the stage for the report, providing context, stating the purpose, and highlighting the significance of the topic.
5. Methodology
In research-oriented reports, the methodology section explains the approach taken to gather data, conduct experiments, or perform studies.
6. Findings
The findings section presents the data collected or the results of the research in a clear and organized manner, often using tables, graphs, or charts.
7. Discussion
The discussion section interprets the findings, provides insights, and offers explanations for observed patterns or trends.
8. Conclusion
The conclusion summarizes the main points, draws conclusions based on the findings, and may include recommendations for future actions.
9. Recommendations
In reports with actionable outcomes, the recommendations section suggests specific steps or strategies based on the findings.
10. References
The references section lists all the sources cited in the report, ensuring proper acknowledgment of external work and adding credibility.
Writing Tips for an Effective Sample Report
Creating a compelling report requires not just proper structure but also excellent writing skills. Here are some valuable tips to enhance your report writing:
1. Know Your Audience
Understanding your target audience is crucial when writing a report. Tailor your language, tone, and content to suit the reader’s level of expertise and interest.
2. Use Clear and Concise Language
Keep your writing clear, straightforward, and to the point. Avoid jargon and unnecessary technical terms that may confuse readers.
3. Organize Information Logically
Present information in a logical sequence, ensuring that each section flows smoothly into the next. Use headings and subheadings to provide a clear structure.
4. Support Claims with Evidence
Back up your statements with credible evidence and data. This adds credibility to your report and strengthens your arguments.
5. Edit and Proofread Thoroughly
Always review your report for grammar, spelling, and punctuation errors. A well-edited report shows professionalism and attention to detail.
6. Seek Feedback
Before finalizing your report, seek feedback from colleagues or peers. Fresh perspectives can help identify areas of improvement.
Selecting Engaging Report Writing Topics
Choosing the right topic is essential for crafting a compelling report. Whether it’s for academic, business, or research purposes, an engaging topic will capture the reader’s interest and keep them invested in your report. Here are some inspiring report writing topics:
1. The Impact of Technology on Modern Workplace s
Explore how technology has transformed traditional workplaces, affecting productivity, communication, and employee satisfaction.
2. Environmental Sustainability in Urban Cities
Examine the efforts made by urban cities to promote environmental sustainability, including green initiatives and waste reduction strategies.
3. The Rise of E-Learning: A Comprehensive Analysis
Analyze the growth of e-learning platforms, their effectiveness in education, and their potential to revolutionize the traditional learning system.
4. Cybersecurity Threats and Mitigation Strategies for Businesses
Investigate the latest cybersecurity threats faced by businesses and outline effective strategies to safeguard sensitive data and prevent cyber attacks.
5. Mental Health in the Workplace: Strategies for Employee Well-Being
Discuss the importance of addressing mental health issues in the workplace and propose strategies to support employee well-being.
Real-World Examples of Impactful Reports
To gain a deeper understanding of report writing’s practical applications, let’s explore some real-world examples:
1. World Health Organization (WHO) – Global Health Report
The WHO publishes comprehensive reports on global health issues, providing data on disease outbreaks, vaccination rates, and healthcare access worldwide. These reports play a crucial role in shaping global health policies and initiatives.
2. McKinsey & Company – Industry Research Reports
Management consulting firm McKinsey & Company produces insightful industry research reports that analyze market trends, consumer behavior, and business strategies. These reports serve as valuable resources for executives and decision-makers.
3. Intergovernmental Panel on Climate Change (IPCC) – Climate Assessment Reports
The IPCC releases periodic reports on climate change, assessing its impacts, causes, and potential solutions. These reports are instrumental in guiding environmental policies and international climate agreements.
A Sample Report Writing Format on A Bank Robbery.
The following points will make it easy to write a report easily shown below.
( Heading) DARING BANK ROBBERY
( Who Reported ) By a Special Correspondent
Where, When, What: Kolkata, August 14 (Introduction): A daring (CART) robbery took place today at 3 p.m. at the United Bank of India, Gariahat Branch, Kolkata.
How, why, Casualty: According to the Branch Manager, three men armed with pistols overpowered the security staff and locked the gate from the inside. One of the miscreants (710) herded the customers and the staff into one corner of the bank and kept them silent at gunpoint. The other two miscreants snatched the keys from the Manager.
Condition: Then they unlocked the vault and bagged cash and jewelry worth Rs. 40 lacks. They came out of the bank hurling bombs, jumped into a black Maruti Van, and sped away.
Reaction & Measures Taken (Conclusion): The police arrived within half an hour. No one has been arrested yet. Investigations are on, as the Deputy Commissioner of Police told the media.
People may also like
Report writing types in english:.
Basically, Report writing in English is of three types .
- General Report Writing: These reports give an account of a person’s experience of an event or an incident.
- Newspaper Report Writing: Newspaper reports are based on true incidents or accidents meant to express some information to the public.
- Business Report Writing: Business reports are made on orders based on observation, investigation, and analysis.
General Report Writing Examples
Example 1: Business Report – Market Analysis
Title: Market Analysis for XYZ Company’s Product Expansion
Executive Summary: The market analysis report assesses the potential of XYZ Company to expand its product line into a new market segment.
Introduction: This report aims to investigate the feasibility and potential challenges associated with XYZ Company’s entry into the youth-oriented consumer electronics market.
Methodology: Data was collected through a combination of surveys, focus groups, and secondary research from reputable industry reports.
Findings: The youth-oriented consumer electronics market is growing rapidly, with an annual growth rate of 12% over the past three years.
XYZ Company’s brand recognition is relatively low among the target audience.
The price sensitivity of the target market is a significant factor to consider.
- Analysis: The findings suggest that while there is a lucrative opportunity for XYZ Company to enter the market, it will require a focused marketing campaign and competitive pricing strategies to overcome initial brand awareness challenges.
- Discussion: By leveraging social media and influencers, XYZ Company can effectively reach the target audience and build brand loyalty. Additionally, offering a competitive pricing model will attract price-conscious customers.
- Recommendations:
- Collaborate with popular influencers to gain credibility and reach a wider audience.
Offer attractive introductory pricing and discounts to entice price-sensitive customers.
Conclusion: Entering the youth-oriented consumer electronics market presents a promising opportunity for XYZ Company. By implementing the recommended strategies, the company can capitalize on this potential growth and expand its product line successfully.
Remember that the specific format and content of a report may vary based on the requirements set by your institution, organization, or supervisor. Always check for any specific guidelines before starting your report writing.
Write a newspaper report on the “Annual Prize Distribution Ceremony in your school”
Annual Prize Distribution Ceremony in your school
By Staff Reporter
[City, Date]: The air was abuzz with excitement and anticipation as [Your School Name] hosted its grand Annual Prize Distribution Ceremony yesterday. The event, held in the school auditorium, was a momentous occasion that celebrated the academic excellence and achievements of the students.
Distinguished guests, parents, and faculty members graced the ceremony with their presence. The school principal, in his opening address, emphasized the significance of recognizing and applauding students’ efforts beyond academics.
The highlight of the event was the distribution of prizes to the meritorious students, acknowledging their outstanding performance in academics, sports, and extracurricular activities. The audience erupted with applause as the achievers walked up the stage to receive their awards.
The melodious music, vibrant dances, and thought-provoking skits captivated the audience.
The Annual Prize Distribution Ceremony concluded on a high note, leaving everyone inspired and motivated. It served as a testament to the school’s commitment to nurturing holistic development among its students.
[Your School Name] once again proved that it is not only a center of academic excellence but also a platform for nurturing well-rounded individuals.
By [Your Name]
Write a newspaper repot on “A terrible fire broke out in Kolkata”
Terrible fire breaks out in kolkata, causing extensive damage.
Kolkata, Date: A devastating fire broke out in a commercial area of Kolkata yesterday, causing widespread destruction and panic among residents and businesses. The incident occurred in the bustling market district, engulfing several multi-story buildings.
Eyewitnesses reported that the fire started in one of the shops due to an electrical short circuit and quickly spread to nearby establishments. Despite the immediate response from firefighters, the blaze proved challenging to control, as narrow streets hindered their access.
Local authorities and emergency services rushed to the scene, evacuating people from nearby buildings and providing medical assistance to those affected. Tragically, a few individuals sustained minor injuries in the process.
The fire caused extensive damage to properties, resulting in significant financial losses for business owners. The full extent of the damage is yet to be assessed.
Investigations into the incident are underway to determine the exact cause and potential safety lapses. As the city mourns the loss of properties and livelihoods, efforts are being made to extend relief and support to the affected residents.
1. Write a report for a newspaper about A Terrible Train Accident.
Odisha Train Accident / Coromandel Express Train Accident
Balasore, 3rd June 2023: At around 7 pm, 2nd June on Friday evening 10-12 coaches of the Shalimar-Chennai Coromandel Express derailed near Baleswar and fell on the opposite track. After some time, another train from Yeswanthpur to Howrah dashed into those derailed coaches resulting in the derailment of its 3-4 coaches. The train crash involving two passenger trains and a goods train in Odisha’s Balasore on Friday is said to be one of the deadliest rail accidents in India. More than 230 people have lost their lives in the accident and 900 have been injured. NDRF, ODRAF, and Fire Services are still working to cut the bogie and try to recover the living or the dead. Local people were seen helping the teams responsible for rescue and relief operations and they queued up to donate blood for the injured in Balasore. As a result, Local people became able to rescue 200-300 injured people A high-level committee has been declared to conduct an inquiry into the train accident. The Centre has announced an ex-gratia compensation of Rs 10 Lakh each to the kin of the deceased and Rs 2 Lakh to grievous and Rs 50,000 for minor injuries, Union Railways Minister Ashwini Vaishnav said.
2. Write a report for a newspaper about A Magic Show .
By Anik Dutta
On Friday, November 18: our school authority invited a magician to surprise the students of the school with a magic show. The magic show was a gift to the students from the school’s authoritative body as the school won the award for Best Disciplined School in Kolkata for the year 2015. The magic show was organized on the school’s open-air stage. The show went on for 2 hours, from 12 to 2 pm. The first magic shown by the great magician was pulling out of a rabbit from his hat which was absolutely empty when he wore it. The spectators were pleasantly surprised. He showed exciting magic tricks one after the other and ended the show with a message to the awestruck students, ‘Practice maths well, and you can do magic too as it is nothing but a game of calculation’. The show was immensely appreciated by all.
3. Write a report for a newspaper about Health Issues of the people of your District .
Health Issues of the People of Your District
By Ravi Yogi
On 20 May 2021: a health awareness campaign camp was organized in the Howrah district by the World Health Organisation. Some volunteers were chosen, who from then on, visit each house every month to remind people to get their children vaccinated. People now follow their instructions and keep their surroundings clean to avoid certain diseases. The volunteers distributed water purifiers at a cheap rate so that people could use them to get pure water. The mosquito-repellant sprays are used every month and mosquito nets are now used to keep mosquitoes away. If the volunteers arrange a blood donation camp every month it could help the people in need. Also, a free health checkup camp could be arranged for further health improvement of the people of the locality.
4. Write a report for a newspaper about the Annual sports Event of Your School .
Annual Sports Event of Your School
By Anwesha Das
The annual sports day of our school (St. Agnes H.S. School) was held on February 15 for the junior students at the school grounds. The event for the junior students started at 9:30 in the morning with a relay race. The next race they had was a tricycle race and the last one the junior students had was a treat to watch. The junior ones’ had to run wearing long gowns and they had to run the track without falling even once.
The juniors enjoyed the fun sporting events a lot, while the visitors’ race involving the parents remained the highlight of the day. At the end of the program Chief Guest Sourav Ganguly gave away the awards to the winners and the class teacher of each class distributed a box containing candies, a chocolate pastry, an orange, and two vanilla cream-filled wafer biscuits to every pupil of her class. The event turned out to be a joyful one with a smile on everyone’s face.
Newspaper Report Writing : Format, Topics, Examples
5. write a newspaper report on the first downpour of the season ..
FIRST DOWNPOUR OF THE SEASON
Kolkata, June 13: Today Kolkata experienced its first downpour during the season. The showers were brought about by a deep depression over the Gangetic West Bengal. There was incessant (WESO) rainfall accompanied by thunder and lightning. In Kolkata, it rained throughout the day with occasional breaks. The weather office at Alipore has recorded a rainfall of 20 cm. Many low-lying areas went underwater. Some of the major roads were waterlogged for several hours. There were traffic jams on many roads. The hand-pulled rickshaws had stopped. Train and air services were disrupted. There were cable faults in many parts of the city. Two persons were electrocuted. But they have not yet been identified, said the police officials.
6. As a Reporter for an English daily, write a report about A violent cyclonic storm .
A VIOLENT CYCLONIC STORM
By a Special Correspondent
Katak, August 12: A violent cyclonic storm ravaged the coastal areas of Odisha today. The cyclone started at about 6.45 p.m. It was said to have rushed at a speed of 80 km per hour. The worst-affected areas include Puri, Baleswar, and Paradip. The cyclone raised the sea to an alarming height. The high tidal waves submerged the low-lying coastal areas. It caused incalculable damage to life and property. More than 10,000 people were rendered homeless. Train services were totally disrupted. The State Government sent its rescue team along with central paramilitary forces to tackle the situation. A sum of Rs. 3 crores has been sanctioned for the relief and rehabilitation of the cyclone-hit people.
7. Write a report for a newspaper about A Serious Road Accident
A Serious Road Accident
Kolkata, January 18: As many as 20 persons including two women and a child were injured in an accident at about 8 pm, on M, G, Road yesterday. The accident took place when a speeding minibus, in a bid to overtake a private bus, skidded off the road. The vehicle carrying 45 passengers went straight into a shopping mall, after breaking the roadside railing, Persons inside the mall and the bus suffered serious injuries Local people started the rescue operation. The injured were taken to the nearest hospital. Locals got agitated and blocked the road causing the suspension of traffic for more than 3 hours. However, the police came and brought the situation under control.
8. Write a report within 100 words for an English daily about Cyclone hitting Coastal West Bengal .
Cyclone hits Coastal West Bengal
-By a Staff Reporter
Kolkata, June 12, 2013: A severe cyclone with a speed of 80 km. per hour hit the coastal areas of West Bengal yesterday evening at about 6-45 p.m. Caused by a deep depression in the Bay of Bengal, the cyclone ripped through the state resulting in huge damage to life and property. 60 persons have died and thousands have been rendered homeless. Train services have been disrupted leaving a number of people stranded. The state government has taken immediate steps to provide relief to the victims. More than 5000 people have been evacuated to temporary relief shelters. The Chief Minister has reviewed the situation and assured the people of all help.
9. Write a newspaper report on a road accident within 100 words .
BRAKE FAILURE BUS COLLIDES WITH A TRUCK
By a Staff Reporter
Kolkata, October 1, 2015: Yesterday at around 10:30 am an accident took place at Sinthi More when an Esplanade bound bus, of route no 78/1, suddenly collided with a truck. The report says the brake failure of the bus was the cause of this mishap. Five passengers were injured including a child and a woman. According to passengers, the ill-fated bus was moving at a great speed. Near Sinthi More the driver lost control and banged behind a truck. Local people rushed in, and took the injured to the nearest hospital where they were released after first aid. Traffic got disrupted. Cops reached the spot quickly, intervened, and normalcy was restored within an hour.
10. Write a report on a Railway accident.
A MAN DIED IN A RAILWAY ACCIDENT
By Kishore Ganguli
Kolkata, April 25: A man died after he had been hit by a Sealdah bound train close to Barrackpore station around 5.40 am today when the victim was returning home from a regular morning walk. According to an eyewitness, the man was trying to cross the tracks, got confused, and ended up on the track on which the train was coming on. Being hit on his head, he was hospitalized immediately. But the doctors declared him dead. The locals made a blockade on the railway tracks. The police came, dispersed the irate mob and the train service was restored. The railway authorities announced an exgratia payment of Rs 2 lakh to the next of kin of the deceased. The situation is tense till now.
FAQs about Report Writing
Q: what is the ideal length for a report.
Reports can vary in length depending on their purpose and complexity. However, a concise report of 10-20 pages is often preferred to keep the reader engaged.
Q: Can I use bullet points in my report?
Yes, using bullet points can enhance readability and make key information stand out. However, use them sparingly and only when appropriate.
Q: Should I include visuals in my report?
Yes, incorporating relevant visuals like graphs, charts, and images can make complex data easier to understand.
Q: Can I include my opinion in the report?
While reports should be objective and fact-based, there might be instances where your expert opinion is valuable. If so, clearly distinguish between facts and opinions.
Q: How can I make my executive summary compelling?
The executive summary should be concise yet informative. Highlight the most important findings and recommendations to pique the reader’s interest.
Q: Is it necessary to follow a specific report writing style?
Different organizations or fields may have their preferred report writing style. Always follow the guidelines provided by your institution or industry standards.
Q: What is the main purpose of a report?
A: The main purpose of a report is to present information, findings, and recommendations in a structured and organized manner.
A: Yes, bullet points can help present information concisely and improve readability.
Q: How long should an executive summary be?
A: An executive summary should be concise, typically ranging from one to two pages.
Q: Is it necessary to include visuals in a report?
A: Including visuals such as charts, graphs, and images can enhance the reader’s understanding of complex data.
Q: What are some common mistakes to avoid in report writing?
A: Common mistakes to avoid include using overly technical language, neglecting to cite sources properly, and lacking a clear structure.
Q: How can I make my report more engaging?
A: To make your report engaging, use real-life examples, incorporate visuals, and use a conversational tone when appropriate.
Enter Your Details

- Project Process
- CSR Activity
PG Projects
- Artificial Intelligence
Image Processing
- Embedded applications
- Industrial Automation
- Deep Learning
- Machine Learning
- Mechatronics
Controllers
- Raspberry pi
- NVIDIA Jetson Nano
- Embedded with Matlab
- Artificial Neural Network
- Image Segmentation
- Image Enhancement
- Image Denoising
- Stegnography
- Fusion and Saliency
- Image Retrieval
- Communications
- MIMO Transmissions
- Device-to-Device Communications
- 5G networks
- Modulation Techniques
Wireless Sensor Networks
- Routing Concepts
Signal Processing
- Patch Antenna
Front End Domains
- Arithmetic Core
- Communications and Crypto Core
- Design for Testability
- Nano Technology
Back End Domains
- Low Power VLSI
- Transistor Logic
- Core Memories
- Cadence EDA
- Xilinx Vivado
- Matlab Interfacing
- Power Systems
- Solar Power Generation
- Wind Power Generation
- Power Quality
- Hybrid Systems
- Distribution Systems
- Power Electronics
- AC-DC Converters
- AC-AC Converters
- DC - AC Converters
- DC - DC Converters
- Multilevel Converters
- Electrical Drives
- Electrical Vehicles
- Control Systems
- Data Mining
- Cloud Computing
- Data Science
- Mobile Computing
- Service Computing
- Secure Computing
- CyberSecurity
- Parallel and Distributed System
- Software Engineering
- Intrusion Detection System
- Wireless Communication
Gaming Projects
Ug projects, major projects, ieee major projects.
- Image Detection
- Image Compression
- Security Applications
- Finite State Machines
Application Major Projects
- Arduino+Python
- Graphical User Interface(GUI)
Interfacing
- Web Applications
- Kotlin Android
- Android Application
Full Stack Projects
- Spring Boot + HTML
- Node.js + React
- Python + Angular
- Python + React
- Node.js + HTML
- Node.js + Angular
- ASP.NET + HTML
- Spring Boot + Angular
- Spring Boot + React
Minor Projects
Inter | diploma projects, school projects, make in india.
- Transportation
- Electronics Developments
- Electricity
- Security & Surveillance
- Current issues
- Smart communication
- Waste management
- Robotics & drones
Digital India
- Smart vehicle
- Renewable Energy
Swasth bharath
- Agriculture & rural developments
- Health care & biomedical
- Food Technology
- Clean Water
- Earth and Environmental Science
Swatch bharath
Phd projects international assignments workshops training internships quick pay sign up login.
2023 B.Tech Final Year Projects for Students

We are South India’s largest edu-tech company and the creator of a unique and innovative live project making platform for students, engineers and researchers.
Want to share this article?
B.Tech is one of the professional courses that many students tend to take up and pursue these days. For successfully completing such a professional course, every student needs to submit their mini project and final year project with utmost care. So, we will discuss the final year as well as the mini projects for BTech students to refer and start doing your projects on your own. Do note that, this article will be primarily focus more on three B.Tech. disciplines like Computer Science, Electronics and Communications, and Electricals and Electronics Engineering.
What are the major Disciplines of B.Tech Projects ?
Though are many disciplines available under the aegis of B.Tech. course, the following are the most important disciplines based on the interests of students over the nation:
Computer Science Engineering
Electronics and Communications Engineering
Electricals and Electronics Engineering
Aerospace Engineering
Mechanical Engineering
Biotechnology Engineering
Civil Engineering
Aeronautical Engineering
Information Technology
How do you proceed with B.Tech Projects ?
To help you in proceeding with B Tech Final Year Projects or mini projects of your choice, we have given the following tips:
Always tend to choose a project domain/ area that interests you most and do not choose your project domain/ area just because your friend chooses.
Start exploring and gathering good quality research manuscripts so that you get better sources before starting your actual project.
Look for practical issue after reading manuscripts of your interest area, so that you can look for the possible solution by successfully executing your idea for project.
Now, it’s time to select your best companion for doing the project with you and then decide on who should be your guide for support your project idea and execution part of it.
Always, be ready with a prior strategy for your project so that any last-minute hurry can be avoided.
Always, do investigation at each phase of your project so that any uncertainties get removed at the earliest possible.
Get a help of any project center who might help you if you are stuck in any part of your project only on your risk.
Prepare a draft of the project report and improvise it in every possible way by getting the inputs from your mates, guide, etc.
Prepare the presentation of your project in the best possible in the way that it’s able to demonstrate the importance of your carried-out project.
B.Tech Final Year Projects
In this section, we will see the three major disciplines of B.Tech. course in India while we discuss B Tech Final Year Projects . For each B.Tech. discipline, various project genres/ domains have been kept in mind while curating the B Tech Final Year Projects for you.
Computer Science BTech Projects
Several Computer Science-based projects for BTech students have been given below by concentrating on several genres like machine and deep learning, Java, Python, Android, etc.
Deep Analysis of Autism Spectrum Disorder Detection Techniques
Electricity Price Forecasting for Cloud Computing Using an Enhanced Machine Learning Model
Novel XGBoost Tuned Machine Learning Model for Software Bug Prediction
Detection of Chronic Kidney Disease using Machine Learning and Deep Learning Algorithms
Deep Learning For Large-Scale Traffic-Sign Detection And Recognition COVID-19 Future Forecasting Using Supervised Machine Learning Models
A Comparative Approach to Predictive Analytics with Machine Learning for Fraud Detection of Realtime Financial Data
An Experimental Study for Software Quality Prediction with Machine Learning Methods
CLEMENT: Machine Learning Methods for Malware Recognition Based on Semantic Behaviours
Predicting Flight Delays with Error Calculation using Machine Learned Classifiers
Comparative Analysis of ML Algorithms for Drought for Prediction
Hazard Identification and Detection using Machine Learning Approach
Machine Learning based Rainfall Prediction
Organization Faults Maintenance System
Deep Learning Based Deforestation Classification
Track&go A Location Prediction Web Application
Deep Learning for Plant Species Classification
Animal Detection in Farms Using OpenCV
Image-Based Plant Disease Detection: A Comparison of Deep Learning and Classical Machine Learning Algorithms
Transfer Learning for Recognizing Face in Disguise
Travel Management System
On the Feasibility of Deep Learning in Sensor Network Intrusion Detection
Classification of Poetry Text Into the Emotional States Using Deep Learning Technique
Machine Learning Algorithm For Brain Stroke Detection
Web Based Database And Sms To Facilitate Health Care Medical Emergency
Deep learning for Classification and Localization of COVID-19 Markers in point-of-care Lung Ultrasound
Deep Learning in Ultrasound Imaging
Online Loading Management System
Deep Facial Diagnosis: Deep Transfer Learning From Face Recognition to Facial Diagnosis
Instant Plasma Donor Recipient Connector Web Application
Deep Learning for Natural Language Parsing
Cloud Data Audition Techniques with a Privacy and Security Focus
Transfer learning-based Object Detection by using Convolutional Neural Networks
Web Application for Breast Cancer Prediction
Deep Learning Based Fusion Approach for Hate Speech Detection
Student Help Desk
Advanced Prediction of Performance of A Student in An University using Machine Learning Techniques
Biometric Based Exam Gate Authentication System With Sms Alert
Anemia Estimation for Patients Using a ML Model
Banking Transaction System using Encryption and Decryption
Mail Tracker
Classification of Electromyographic Hand Gesture Signals Using Modified Fuzzy C-Means Clustering and Two-Step Machine Learning Approach
Accurate Newspaper Article Classification Using Multi-Class Support Vector Machine
Daily Pulse of Covid-19
Analysis for Disease Gene Association Using Machine Learning
Anonymous Traceble Group data sharing in Cloud Computing
Fraud Detection in Credit Card Data using Unsupervised Machine Learning Based Scheme
HealthCare Chatbot System
Learning Deep Gradient Descent Optimization for Image Deconvolution
Evaluation of Deep Learning Techniques in Sentiment Analysis from Twitter Data
Village Development System
Sentiment Classification from Text Using Deep Learning Algorithm
Identification of Plant Nutrient Deficiencies Using Convolutional Neural Networks
Online Retail Management System
Construction of Machine-Labeled Data for Improving Named Entity Recognition by Transfer Learning
Web Server Management System
Covid Patients Tracing Web Application
Detecting and Characterizing Extremist Reviewer Groups in Online Product Reviews
E-calculator For Calorie Calculating And Provide Suggestions
Rice Leaf Diseases Classification Using Cnn With Transfer Learning
Put A QRcode in Your ClassRoom
A Novel Ensemble Learning Paradigm for Medical Diagnosis With Imbalanced Data
Consumer Sales Online Fake Review Detection and Deletion
Noise Suppresed Image Enhancing Environment
E-Blood Bank Monitoring Hospitals
Improvement in Automated Diagnosis of Soft Tissues Tumors Using Machine Learning
Conducting Exams with Different Sets and Create Hall Tickets with QR Code
Research on Medical Image Classification Based on Machine Learning
E-singers Online Rank Providing for Singers Based on Songs
Analysis of Facial Sentiments: A Deep-learning Way
Student Grievance Support System
Image Denoising via Sequential Ensemble Learning
E-Assessment and Evaluation
Deep Convolution Neural Network for Big Data Medical Image Classification
Company employee profile using QR code
Accurate Short Text Classification using Bi-LSTM
Emotion Recognition using Speech Processing
Privacy Preserving Data Processing with Flexible Access Control
Stock Price Prediction using DL
Desktop Supermarket Application
Covid-19 predictor using X-Ray Images Analysis
Performance Analysis on Student Feedback using Machine Learning Algorithms
Buy-Sell Exchange Automobiles using the Android Application
Smart Library Management
Navigation And Obstacle Detection For Visually Impaired
Text and Image Encryption Decryption Using AES Algorithm
Psychology Chatbot
Android Based Student Fees details Application
Analyzing of Product Reviews using Sentimental analysis
Personality analyzer
Customer Segmentation
Handwritten Character Recognition System
Home Automation For Disabled Persons Using His Voice Tag
Deep Learning for Weed and Crop Classification
Automatic Seating Arrangements
Also check : ECE Final Year Project Ideas 2022
Electronics and Communication-based BTech Projects
This sub-section deals majorly ECE based B Tech Final Year Projects revolving around IEEE/ VLSI and IEEE/ECE projects.
Accuracy-Configurable Radix-4 Adder with a Dynamic Output Modification Scheme
Low Power High Performance 4-bit Vedic Multiplier in 32nm
Design of Approximate Multiplier less DCT with CSD Encoding for Image Processing
A Low-Power and High-Accuracy Approximate Multiplier With Reconfigurable Truncation
High performance IIR filter implementation on FPGA
A Comparative Study of LoRa and IEEE 802.15.4-based IoT Deployments inside School Buildings
A New Energy-Efficient and High Throughput Two-Phase Multi-Bit per Cycle Ring Oscillator-Based True Random Number Generator
Approximate Pruned and Truncated Haar Discrete Wavelet Transform VLSI Hardware for Energy-Efficient ECG Signal Processing
IoT Based Real-Time Remote Patient Monitoring System
SAM: A Segmentation based Approximate Multiplier for Error Tolerant Applications
An Efficient and High-Speed Overlap-Free Karatsuba-Based Finite-Field Multiplier for FGPA Implementation
An intelligent baby monitoring system based on Raspberry PI, IoT sensors and convolutional neural network
Optimal Architecture of Floating-Point Arithmetic for Neural Network Training Processors
High performance IIR flter implementation on FPGA
Facial and Voice Recognition Based security and Safety System in Car
A Three-Stage Comparator and Its Modified Version With Fast Speed and Low Kickback
Design and Analysis of IoT-Based Intelligent Robot for Real-Time Monitoring and Control
Low Power, High Performance PMOS Biased Sense Amplifier
Low power Smart Vehicle Tracking, Monitoring, Collision avoidance and Antitheft System
The Constant Multiplier FFT
Development of congestion level based dynamic traffic management system using IoT
Power Efficient Clock Pulsed D Flip Flop Using Transmission Gate
A High-Performance Multiply-Accumulate Unit by Integrating Additions and Accumulations into Partial Product Reduction Process
Hardware Root Of Trust for IoT Security In Smart Home Systems
Data Flow Obfuscation: A New Paradigm for Obfuscating Circuits
Towards Real-Time Eye blink Detection in the Wild: Dataset, Theory and Practices
Design of Low-Power Wallace Tree Multiplier Architecture Using Modular Approach
A Compact FPGA-Based Accelerator for Curve-Based Cryptography in Wireless Sensor Networks
Analysis of High Speed Hybrid Full Adder
A Novel Approximate Adder Design using Error Reduced Carry Prediction and Constant Truncation
Approximate Adiabatic Logic for Low-Power and Secure Edge Computing
A Reliable Approach to Secure IoT Systems using Cryptosystems Based on SoC FPGA Platforms
Ultra-Efficient Nonvolatile Approximate Full-Adder with Spin-Hall-Assisted MTJ Cells for In-Memory Computing Applications
Electrical and Electronics-based BTech Projects
This sub-section considered genres like Power systems, Power electronics , and many more like this to curate the electrical and electronics based B Tech Final Year Projects list for you.
Solar Power Generation System with Power Smoothing Function
Multiphase Interleaved Converter Based on Cascaded Non-Inverting Buck-Boost Converter
Movement Sensed Automatic Door Opening System
A Generalized High Gain Multilevel Inverter for Small Scale Solar Photovoltaic Applications
Pic Based Density Based Traffic Signal System
Power Quality Enhancement of the Distribution Network by Multilevel STATCOM-Compensated Based on Improved One-Cycle Controller
A Unified Active Damping for Grid and Converter Current Feedback in Active Front End Converters
A Grid Frequency Support Control Strategy of the Three Phase Cascaded H Bridge Based Photovoltaic Generation System
Control and Management of Railway System Connected to Microgrid Stations
Wireless Mobile Charging Project
Investigations On Shunt Active Power Filter In A Pv-wind-fc Based Hybrid Renewable Energy System To Improve Power Quality Using Hardware-in-the Loop Testing Platform
Energy Management Strategy of AC DC Hybrid Microgrid Based on Solid State Transformer
Modeling and Control of Single-Stage Quadratic-Boost Split Source Inverters
Effective Grid Connected Power Injection Scheme Using Multilevel Inverter Based Hybrid Wind Solar Energy Conversion System
A Novel and High Gain Switched Capacitor and Switched Inductor Based DC DC Boost Converter with Low Input Current Ripple and Mitigated Voltage Stresses
High Efficiency and Voltage Conversion Ratio Bidirectional Isolated DC-DC Converter for Energy Storage System
Design and Cascade PI Controller-Based Robust Model Reference Adaptive Control of DC-DC Boost Converter
Also check : IEEE Projects for EEE Students
Major disciplines for Mini Project for BTech
After completing the comprehensive final year project titles for B.Tech . course, we now move onto the Mini Project for BTech in this section. Just like the final year project listings, we are taking the same disciplines of B.Tech. course like Computer Science, Electronics and Communications, and Electricals and Electronics Engineering.
Computer Science B.Tech Mini Projects
This sub-section deals with the mini project genres like Python, Android, Open CV, PHP, Java, etc. for mini projects for BTech students revolving around computer science-based course.
SMART GYM
Medical Assistance Using OCR
Smart Electronic Voting Machine with Face Recognition using Raspberry Pi
E-Mentoring
Agriculture Apps
Online Portal for Agri Business
A System Which Converts Text in Voice
COVID-19 Monitor(Real time mask detector)
Hall Ticket Generator with QR code
Corporate Recruitment System
Design of Sensing Soil Moisture Content By Auto Irrigation System
Online Property Management System
Online Rehashed Books Store System
Real Time Smart Attendance Monitoring System With Image Processing And Thermal Scanning
Online Toll Payment System
Smart Parking Solutions for On-Street and Off-Street Parking
Tracking College Buses
Human Emotion Detection Using Open CV
Home services
Insight:Effective way of Knowledge Sharing
Vehicle Speed Detection using Machine Learning Approach
Course Recommendation System
Detect People in a Frame Using Raspberry Pi with Open CV
Android Based Vehicle Mechanic System
Smart Home with Wireless Smart Doorbell with Smart Response
Student Information Chat Bot
Smart Fish Aquaculture Monitoring System with Water Color Identification Using Mobile Camera
Green Image Segmentation Analysis of Google Earth to Rank World Universities using PHP and MATLAB
Hands Together
Online Hostel Food Waste Management System
University Admission Management System
Automatic Backup Application for Organisation
College Information System
Electronics and Communication-based B.Tech. Mini Projects
This sub-section deals with the project genres like VLSI, WSNs- Wireless Sensor Networks, Embedded Systems, Communication, etc. for mini projects revolving around B.Tech. ECE course. Over 25 mini project titles have been given below for you.
Performance Analysis of Wallace Tree Multiplier with Kogge Stone Adder using 15-4 Compressor
Power-Efficient Approximate SAD Architecture with LOA Imprecise Adders
Binary to Gray Code Converter Implementation using QCA
Area and Power Efficient VLSI Architecture of Distributed Arithmetic Based LMS Adaptive Filter
Energy-Efficient Approximate Multiplier Design using Bit Significance-Driven Logic Compression
Image and Video Processing Applications using Xilinx System Generator
Design and Simulation of CRC Encoder and Decoder using VerilogHDL
Chip Design for Turbo Encoder Module for In-Vehicle System
Efficient Implementations of 4-Bit Burst Error Correction for Memories
Low Power 1-Bit Full Adder using Full-Swing Gate Diffusion Input Technique
Area–Delay–Power Efficient Carry-Select Adder
Machine Learning Based Power Efficient Approximate 4:2 Compressors for Imprecise Multipliers
Design of High Speed Carry Select Adder using Brent Kung Adder
A Low Power Reconfigurable LFSR
Scalable Construction of Approximate Multipliers with Formally Guaranteed Worst Case Error
Logic Synthesis in Reversible PLA
Low-Power Approximate MAC Unit
A Novel Data Format for Approximate Arithmetic Computing
Design of Low Power Magnitude Comparator
Area-Delay Efficient Binary Adders in QCA
Smart Event Invitation
Agriculture Updates Android Project
Android File Storage
Panic Control
On Road Vehicle Assistance Finder
Anti-Ragging App
Android Habit Tracker
College Notification Voice Alerts
Electrical and Electronics-based B.Tech Mini Projects
Over 10 mini project titles have been covered in this sub-section by including but not limited to Induction Generating devices, Converters, etc.
Hybrid And Adaptive Sectors P&o Mppt Algorithm Based Wind Generation System
Modeling and Simulation of Incremental Conductance MPPT Algorithm for Photovoltaic Applications
Modeling Of An Intelligent Battery Controller For Standalone Solar-wind Hybrid Distributed Generation System
Maximum Power Point Tracking of Photovoltaic System Using Fuzzy Logic Controller Based Boost Converter
Improved Mppt Method To Increase Accuracy And Speed In Photovoltaic Systems Under Variable Atmospheric Conditions
Reducing Harmonics Distortion in Distribution Network Against the Induction Motor Drive Non Linear Load
Design and Implementation of Maximum Power Point Tracking (MPPT) Algorithm for a Standalone PV System
Fuel Cell Distributed Generation Systems Using Fuzzy Logic Control
Modeling and Simulation of Direct Torque Control Induction Motor Drives via Constant Volt/Hertz Technique
This article had discussed about the major B.Tech. final year as well as the minor project perspective titles by giving you over 200 titles in order to serve as the best guide for anyone who is starting their final year or pre-final year project for completing their B.Tech. course.
How do Takeoff Projects support for any discipline of BTech Projects ?
At Takeoff Projects , they support for all kinds of project needs arising out of the three major disciplines that have been discussed in the article. From the computer science sense, they offer projects in significant genres like Android, Java, NS2, Python, and many other latest trend genres. From the sense of Electronics and Communication, they offer projects in Embedded, VLSI, and MATLAB. For serving the students of Electricals and Electronics courses, they offer projects revolving around many electricals like UPS, Microgrids, Motors, speed controllers, Power Distribution Systems (PDS), Nano grids, Turbines, Oscillation suppressors, Rectifiers, Voltage controllers, and many more. So, if you are anyone who is looking to do the project in any of these, get their support and be successful with your project journey.
Our Trending Blogs

Subscribe to our Blog
Need help in deciding the your academic project.

Related Articles

Ethical Considerations in Image Processing: Balancing Innovation and Privacy
From Pixels to Insights A Journey into Image Enhancement Algorithms

The Role of Convolutional Neural Networks in Medical Image Analysis

Advancements in Image Segmentation Techniques: A Comprehensive Overview

Unraveling the Power of Deep Learning in Image Processing

Importance of Final Year Projects for Students

How to Present Your Final Year Project to Your Supervisor?


How to Choose the Right Final Year Project Topic?

Common Mistakes to Avoid on Your Final Year Project

How to Write a Winning Engineering Project Report?

Low Cost Mini Projects Ideas for Civil Engineering
Low Cost Mini Project Ideas for Mechanical Engineering

BSc IT Projects for Final Year
Instrumentation Projects for Final Year Students
Biomedical Instrumentation Projects
M.Tech Structural Engineering Projects

M.Tech Thesis Writing Services
M.Tech Projects for Electrical, Electronics & Software Engineering
Latest Final Year Projects for B.Tech & M.Tech Students

Latest BCA Final Year Project Ideas for 2023
Top BE Projects Ideas & Topics for Students
14+ Interesting Engineering Projects

IEEE Final Year Projects

Request Call Back
- Call Me Now
- Call Me later
- Leave a Message
Would you like to receive a free callback now?
Choose the best time for callback:, leave your message and we will contact you as soon as possible, get in touch with us, quick links.
- Knowledge Base
- Terms & Conditions
- Privacy Policy
Specialization
Our services.
- Academic Projects
- Internships

+91 9030333433 +91 8776681444
Disclaimer - Takeoff Edu Group Projects, are not associated or affiliated with IEEE, in any way. The IEEE Projects mentioned here are mentioned in the context of student projects, whose ideas are derived from IEEE publications, and not projects of or by IEEE.
©2024 TAKEOFF EDU GROUP All Rights Reserved.
Design & developed by YMTSINDIA
Create Account
Welcome back.
To keep connected with us please login with your personal info
Already Have an Account!!
Hello, Friend!
Enter your personal details and start journey with us

This website requires JavaScript.
Please enable javascript in your brower settings and refresh the page.

25,000+ students realised their study abroad dream with us. Take the first step today
Here’s your new year gift, one app for all your, study abroad needs, start your journey, track your progress, grow with the community and so much more.

Verification Code
An OTP has been sent to your registered mobile no. Please verify

Thanks for your comment !
Our team will review it before it's shown to our readers.

Report Writing
- Updated on
- Nov 4, 2023

The term “report” refers to a nonfiction work that presents and/or paraphrases the facts on a specific occasion, subject, or problem. The notion is that a good report will contain all the information that someone who is not familiar with the subject needs to know. Reports make it simple to bring someone up to speed on a subject, but actually writing a report is far from simple. This blog will walk you through the fundamentals of report writing, including the structure and practice themes.
This Blog Includes:
What is a report, reporting formats, newspaper or magazine reports, business reports, technical reports, what is report writing, report writing: things to keep in mind, structure of report writing, magazine vs newspaper report writing format, report writing format for class 10th to 12th, report writing example, report writing for school students: practice questions, report writing slideshare.
- Report Writing in 7 steps
Also Read: Message Writing
A report is a short document written for a particular purpose or audience. It usually sets out and analyses a problem often recommended for future purposes. Requirements for the precise form of the report depend on the department and organization. Technically, a report is defined as “any account, verbal or written, of the matters pertaining to a given topic.” This could be used to describe anything, from a witness’s evidence in court to a student’s book report.
Actually, when people use the word “report,” they usually mean official documents that lay out the details of a subject. These documents are typically written by an authority on the subject or someone who has been tasked with conducting research on it. Although there are other forms of reports, which are discussed in the following section, they primarily fulfil this definition.
What information does reporting contain? All facts are appreciated, but reports, in particular, frequently contain the following kinds of information:
- Information about a circumstance or event
- The aftereffects or ongoing impact of an incident or occurrence
- Analytical or statistical data evaluation
- Interpretations based on the report’s data
- Based on the report’s information, make predictions or suggestions
- Relationships between the information and other reports or events
Although there are some fundamental differences, producing reports and essays share many similarities. Both rely on facts, but essays also include the author’s personal viewpoints and justifications. Reports normally stick to the facts only, however, they could include some of the author’s interpretation in the conclusion.
Reports are also quite well ordered, frequently with tables of contents of headers and subheadings. This makes it simpler for readers to quickly scan reports for the data they need. Essays, on the other hand, should be read from beginning to end rather than being perused for particular information.
Depending on the objective and audience for your report, there are a few distinct types of reports. The most typical report types are listed briefly below:
- Academic report: Examines a student’s knowledge of the subject; examples include book reports, historical event reports, and biographies.
- Identifies data from company reports, such as marketing reports, internal memoranda, SWOT analyses, and feasibility reports, that is useful in corporate planning.
- Shares research findings in the form of case studies and research articles, usually in scientific publications.
Depending on how they are written, reports can be further categorised. A report, for instance, could be professional or casual, brief or lengthy, and internal or external. A lateral report is for persons on the author’s level but in separate departments, whereas a vertical report is for those on the author’s level but with different levels of the hierarchy (i.e., people who work above you and below you).
Report formats can be as varied as writing styles, but in this manual, we’ll concentrate on academic reports, which are often formal and informational.
Also Read: How to Write a Leave Application?
Major Types of Reports
While the most common type of reports corresponds to the ones we read in newspapers and magazines, there are other kinds of reports that are curated for business or research purposes. Here are the major forms of report writing that you must know about:
The main purpose of newspaper or magazine reports is to cover a particular event or happening. They generally elaborate upon the 4Ws and 1H, i.e. What, Where, When, Why, and How. The key elements of newspaper or magazine report writing are as follows:
- Headline (Title)
- Report’s Name, Place, and Date
- Conclusion (Citation of sources)
Here is an example of a news report:
Credit: Pinterest
Business reports aim to analyze a situation or case study by implementing business theories and suggest improvements accordingly. In business report writing, you must adhere to a formal style of writing and these reports are usually lengthier than news reports since they aim to assess a particular issue in detail and provide solutions. The basic structure of business reports includes:
- Table of Contents
- Executive summary
- Findings/Recommendations
The main purpose of the technical report is to provide an empirical explanation of research-based material. Technical report writing is generally carried out by a researcher for scientific journals or product development and presentation, etc. A technical report mainly contains
- Introduction
- Experimental details
- Results and discussions
- Body (elaborating upon the findings)
Must Read: IELTS Writing Tips
A report is a written record of what you’ve seen, heard, done, or looked into. It is a well-organized and methodical presentation of facts and results from an event that has already occurred. Reports are a sort of written assessment that is used to determine what you have learned through your reading, study, or experience, as well as to provide you with hands-on experience with a crucial skill that is often used in the business.
Before writing a report, there are certain things you must know to ensure that you draft a precise and structured report, and these points to remember are listed below:
- Write a concise and clear title of the report.
- Always use the past tense.
- Don’t explain the issue in the first person, i.e. ‘I’ or ‘Me’. Always write in the third person.
- Put the date, name of the place as well as the reporter’s name after the heading.
- Structure the report by dividing it into paragraphs.
- Stick to the facts and keep it descriptive.
Must Read: IELTS Sample Letters
The format of a report is determined by the kind of report it is and the assignment’s requirements. While reports can have their own particular format, the majority use the following general framework:
- Executive summary: A stand-alone section that highlights the findings in your report so that readers will know what to expect, much like an abstract in an academic paper. These are more frequently used for official reports than for academic ones.
- Introduction: Your introduction introduces the main subject you’re going to explore in the report, along with your thesis statement and any previous knowledge that is necessary before you get into your own results.
- Body: Using headings and subheadings, the report’s body discusses all of your significant findings. The majority of the report is made up of the body; in contrast to the introduction and conclusion, which are each only a few paragraphs long, the body can span many pages.
- In the conclusion, you should summarize all the data in your report and offer a clear interpretation or conclusion. Usually, the author inserts their own personal judgments or inferences here.
Report Writing Formats
It is quintessential to follow a proper format in report writing to provide it with a compact structure. Business reports and technical reports don’t have a uniform structure and are generally based on the topic or content they are elaborating on. Let’s have a look at the proper format of report writing generally for news and magazines and the key elements you must add to a news report:
To Read: How to Learn Spoken English?
The report writing structure for students in grades 10 and 12 is as follows.
- Heading : A title that expresses the contents of the report in a descriptive manner.
- Byline : The name of the person who is responsible for drafting the report. It’s usually included in the query. Remember that you are not allowed to include any personal information in your response.
- (introduction) : The ‘5 Ws,’ or WHAT, WHY, WHEN, and WHERE, as well as WHO was invited as the main guest, might be included.
- The account of the event in detail : The order in which events occurred, as well as their descriptions. It is the primary paragraph, and if necessary, it can be divided into two smaller paragraphs.
- Conclusion : This will give a summary of the event’s conclusion. It might include quotes from the Chief Guest’s address or a summary of the event’s outcome.
Credit: sampletemplates.com
Credit: SlideShare
Now that you are familiar with all the formats of report writing, here are some questions that you can practice to understand the structure and style of writing a report.
- You are a student of Delhi Public School Srinagar handling a campus magazine in an editorial role. On the increasing level of global warming, write a report on the event for your school magazine.
- On the Jammu-Srinagar highway, a mishap took place, where a driver lost his control and skidded off into a deep gorge. Write a report on it and include all the necessary details and eyewitness accounts.
- As a reporter for the Delhi Times, you are assigned to report on the influx of migrants coming from other states of the country. Take an official statement to justify your report.
- There is a cultural program in Central Park Rajiv Chowk New Delhi. The home minister of India is supposed to attend the event apart from other delegates. Report the event within the 150-200 word limit.
- Write today’s trend of COVID-19 cases in India. As per the official statement. include all the necessary details and factual information. Mention the state with a higher number of cases so far.
- In Jawaharlal Nehru Stadium in New Delhi, a table tennis tournament was held between Delhi Public School New Delhi and DPS Punjab. Report the event in 250-300 words.
Also Read: Formal Letter Format, Types & Samples
Credits: Slideshare
Report Writ ing in 7 steps
- Choose a topic based on the assignment
- Conduct research
- Write a thesis statement
- Prepare an outline
- Write a rough draft
- Revise and edit your report
- Proofread and check for mistakes
Make sure that every piece of information you have supplied is pertinent. Remember to double-check your grammar, spelling, tenses, and the person you are writing in. A final inspection against any structural criteria is also important. You have appropriately and completely referenced academic work. Check to make sure you haven’t unintentionally, purposefully, or both duplicated something without giving credit.
Related Articles
Any business professional’s toolkit must include business reports. Therefore, how can you create a thorough business report? You must first confirm that you are familiar with the responses to the following three questions.
Every company report starts with an issue that needs to be fixed. This could be something straightforward, like figuring out a better way to organise procuring office supplies, or it could be a more challenging issue, like putting in place a brand-new, multimillion-dollar computer system.
You must therefore compile the data you intend to include in your report. How do you do this? If you’ve never conducted in-depth research before, it can be quite a daunting task, so discovering the most efficient techniques is a real plus.
Hopefully, this blog has helped you with a comprehensive understanding of report writing and its essential components. Aiming to pursue a degree in Writing? Sign up for an e-meeting with our study abroad experts and we will help you in selecting the best course and university as well as sorting the admission process to ensure that you get successfully shortlisted.
Ankita Mishra
A writer with more than 10 years of experience, including 5 years in a newsroom, Ankita takes great pleasure in helping students via study abroad news updates about universities and visa policies. When not busy working you can find her creating memes and discussing social issues with her colleagues.
Leave a Reply Cancel reply
Save my name, email, and website in this browser for the next time I comment.
Contact no. *

Leaving already?
8 Universities with higher ROI than IITs and IIMs
Grab this one-time opportunity to download this ebook
Connect With Us
25,000+ students realised their study abroad dream with us. take the first step today..

Resend OTP in

Need help with?
Study abroad.
UK, Canada, US & More
IELTS, GRE, GMAT & More
Scholarship, Loans & Forex
Country Preference
New Zealand
Which English test are you planning to take?
Which academic test are you planning to take.
Not Sure yet
When are you planning to take the exam?
Already booked my exam slot
Within 2 Months
Want to learn about the test
Which Degree do you wish to pursue?
When do you want to start studying abroad.
September 2024
January 2025
What is your budget to study abroad?
How would you describe this article ?
Please rate this article
We would like to hear more.
Academia.edu no longer supports Internet Explorer.
To browse Academia.edu and the wider internet faster and more securely, please take a few seconds to upgrade your browser .
Enter the email address you signed up with and we'll email you a reset link.
- We're Hiring!
- Help Center

Guidelines for B.Tech. Project Reports DEPARTMENT OF ELECTRONICS AND COMMUNICATION ENGINEERING GOKARAJU RANGARAJU INSTITUTE OF ENGINEERING AND TECHNOLOGY HYDERABAD 500 090 Guidelines for BTech Project Reports

This document gives a set of guidelines on the format of the B.Tech. project report. Its purpose is to help you prepare and turn in a professional document. These guidelines include complete descriptions of the organization, general considerations and the submission of the report.
Related Papers
ferry husain
Guide to writing paper in ej
- We're Hiring!
- Help Center
- Find new research papers in:
- Health Sciences
- Earth Sciences
- Cognitive Science
- Mathematics
- Computer Science
- Academia ©2024
English: Technical Reporting: Choose a Topic
- Choose a Topic
- Books on Cultural Diversity
- Find Articles
- Find a Video
- Cite Sources
- E-Books & E-Videos for Writing Help
- Websites: Job Research
- OWLs & Other Writing Web Sites
- Request an Information Literacy Session!
- PROWL Tutorial
Writing About the Workplace: Topic Ideas
- Impact of layoffs at work
- Generational differences at work
- Employee burnout
- Executive pay
- Sustainability in workplace
- Fitting in at work
- Employee recognition
- Sustainably designed offices
- Workplace dress codes
- Coworker chemistry
- Employee teams
- Mentoring in the workplace
- Gender differences
- Transgendered employees
- Bullying in the workplace
- Violence at work
- Travel on the job
- Healthy workplaces
- Sexual harassment
- Pay and benefit inequality
- Workplace safety
- Outsourcing the workplace
- Employee and colleague motivation
- Romance and dating on the job
- Disability accommodation at work
- Religious accommodation at work
- 'Foul' language at work
- Breastfeeding at work
- Employee illness
- Employee sexual orientation
- Employees with PTSD
- Politics in the workplace
- Free speech in the workplace
- Nepotism at work
- Sexual orientation at work
- Employee assistance programs
- Work schedules and flexible hours
- Family-friendly scheduling
- Scheduling of part-time employees
- Connectivity in the workplace
- Social media at work
- Drug screening at work
- Identifying leaders at work
- Workplace transparency
- Employee unions
- Hiring veterans
- Work contracts and at-will employment
- Employee privacy on the job
- Employees personal lives and the workplace
- Racial and ethnic minorities in the workplace
- Noise and the workplace
- Discrimination in the workplace
- 'Interns' at work
- Employee turnover
- Employee training and professional development
- Monitoring employees at work (visually and digitally)
Search Credo Reference

Browse for a Topic
- CQ Researcher - Browse Topics Excellent reports on topics related to the U.S.
- Workplace Topics: San Diego Reader
- Opposing Viewpoints - Browse Topics Index Choose from 200+ Topics!
- Communicating with Colleagues and Peers - Inc. Magazine "Communication experts and CEOs share their strategies for smooth communications with employees, making winning presentations to investors, writing and delivering speeches that get standing ovations, and much more."
- Women in the Workplace: Research Guide from Princeton University
- National Partnership for Women and Families
- Safety in the Workplace
- Violence in the Workplace
- Index on Workplace Bullying: WorkplaceViolence911
- Workplace Bullying: A Blog
Paper Topics on the Web
- Midway College - Library's List of 100 Research Paper Topics Browse away!
- Contra Costa College - Topics List Long list also includes common subject headings!
- << Previous: Home
- Next: Find a Book >>
- Last Updated: Apr 3, 2024 7:51 AM
- URL: https://libguides.madisoncollege.edu/English/TechReporting
1701 Wright Street | Madison, Wisconsin 53704 | Libraries: 608.246.6640 | Student Achievement Centers: 608.246.6125 | College Info: 608.246.6100

200 Seminar Topics for Engineering Students
Welcome to the home of all the latest technical seminar topics. Here engineering students can select the best technical seminar topic ideas on the latest technology. A seminar is a form of academic instruction that may be either at a university or a professional organization. The idea behind the seminar system is to familiarize students more extensively with the methodology of their chosen subject and also allow them to interact with the example of practical problems. This article lists technical seminar topics for engineering students.
The following technical seminar topics mainly include technical seminar topics for ECE , technical seminar topics for EEE students.

OLEDs (Organic Light Emitting Diodes)
The term OLED stands for the organic light-emitting diode. In the electronics field, OLED is a new technology. Please refer to this link to know more about OLED Display Technology .
Pill Camera
The camera which is in pill shape is known as a pill camera. This camera can be swallowed by the patient for the treatments of cancer, anemia, and ulcers. This camera travels within the body to capture the inside of the body without harming any parts & sends it to the receiver.
Plastic Solar Cell Technology
The main function of solar cell technology is to convert sun energy into electricity by absorbing sunlight. This cell cannot work in cloudy weather. To overcome this situation, the plastic solar cell was developed. This cell uses the sun’s energy and converts it into electrical even in a cloudy weather condition.
At present, technology like a Bio-chip is a rising technology. This technology is mainly used for diagnosing diseases as well as detects bioterrorists. Please refer to this link to know more about Bio Chip technology
Iris Recognition
This is an automatic technique of biometric identification. This method utilizes the methods of mathematical prototype identification on video images of the iris of a person’s eyes, where the person’s complex prototypes are stable, unique & can be observed from some distance.
Electronic-waste can be defined as electrical otherwise electronic devices that are not usable, which means the devices broken items, working items that are thrown within the trash, etc. If these devices are not sold in the store then it will be not usable. So, E-waste is E-waste is very hazardous because of the toxic chemicals like lead, mercury, cadmium, etc that naturally leak from the metals when they are buried.
Smart Note Taker
A helpful device like a smart note tracker or smartpen is used for taking easy and fast notes of everything. This note can be stored within the memory of the pen. This pen is also used to take note of conversations on the telephone & helps blind people.
This smart device is very helpful for people to satisfy the requirements of busy people in the present busy and technological life. This product is also used to write a note on the air when we are busy with some other work. This note can be stored within the memory of the pen.
Optical Ethernet
In the LAN (local area network), the physical layer is known as optical Ethernet. This is used to transmit the data through fiber optic cable. It is used to connect switches as well as internet servers within data centers, equipment racks & among urban data centers.
At present, the data rate which is used most widely is 1 Gb/s. These are inadequate to hold up core networking necessities like routing, switching, routing & aggregation within huge data centers. To overcome this, optical Ethernet is implemented which is extended from LANS to MANs & WANs.
IBOC Technology
The IBOC (In-band on-channel) is one kind of technique used to transmit the radio signals like analog and digital on the equal frequency without assigning other range.
This kind of technology permits the broadcasting of digital audio without using new range allocations intended for the digital signal. This system will be well-matched with obtainable tuners because it uses the accessible AM &FM bands through connecting a digital sideband signal toward the typical analog signal.
The IBOC technology uses a PAC (perceptual audio coder) for digital compression that is expanded throughout Lucent Technology. A system like USADR AM IBOC DAB includes the FEC (forward error correction), the codec, blender, modem & interleaving section.
A honey pot is a well-made computer system that is used to monitor and focus on the changes made by the hackers in the system. This system is very helpful in imitating likely cyberattack targets. Honeypot can also be used for detecting attacks otherwise prevent them from a valid target & gets the data regarding how cybercriminals work.
E-textile or electronic textile is a cloth material that can be used to conduct electrical energy. It is designed with electronic components to detect the changes in its surroundings & react by turn off the light, radio waves, or sound.
These fabrics include electronics as well as interconnections between them. An E-textile is capable of sensing, communication, interconnection technology & power transmission to permit sensors otherwise things like processing information devices to be connected mutually in a fabric. It gives an overview of the challenges experienced to connect the electronics into the cloth.
Metamorphic Robots
A robotic system is built with a set of mechatronic modules which can be controlled independently. Each module can attach, separate, and mount over contiguous modules. This system can reconfigure dynamically through the locomotion of modules over their neighbors. This kind of robot self configures its outline dynamically without human involvement.
Spectrum Pooling
The strategy of spectrum management is known as spectrum pooling where several radio spectrum users can coexist in a single portion of radio spectrum space. The spectrum or bandwidth of an Electromagnetic Wave is a significant, valuable, and incomplete resource that must be used very cautiously. This is a strategy for sending the RF among two systems exclusive of any clashes.
Embedded Web Server using ARM
The www (World Wide Web) continuously develops through fundamental technologies for simply browsing the web. For different applications, web browsers are used as a standard interface like real-time applications of an embedded system like the Acquisition System of Remote Data. The web server can be developed with the help of HTML and it includes different web pages.
The embedded web server can be developed through embedded c language that is helpful for different applications like mission-critical, ATM, acquisition systems for remote data & controlling devices like DC motor, servo motor, stepper motor, control the stereo sets, use like dimmer stat for controlling intensities of light.
It is used in home automation, used to store programs within flash memory & works based on the requirement. An embedded web server using an ARM processor is helpful in the applications of the agricultural field for monitoring.
Robot for Multipurpose
This multipurpose robot is mainly used in the military as well as civil applications for night security, spying enemy, detecting of leakage gas & rescue operations throughout disasters, etc. This robot can be designed with a wheel system, different sensors, mechanical arms, mechanisms like remote controlling & wireless communication.
Microbivores
The microbivore is a nanomedical device or nanorobot with an oblate spheroidal. This device includes billions of structural atoms which are exactly arranged, mostly water molecules or gas once completely loaded. These robots are inserted in patients for an extensive range of antimicrobial functions.
At present, Barcodes are used everywhere for detection in the process of business. This can be represented in the form of visual, machine-readable, etc. At first, these are signified through changing the spacings and widths of parallel lines.
Polytronics
The silicon industry has influenced the electronic industries. But, technologists at present implementing alternatives mostly like plastic circuits to meet our upcoming requirements. So, polytronics was developed in electronics. It is the study of polymeric materials used within electronics.
As compared with Si technology, it has several benefits like less cost; manufacturing is easy, reused, recycled, uses less power, small, movable & less weight. These are used to design the display devices that have an outstanding quality of the picture. The polytronics play a key role within flexible electronics.
IR Plastic Solar Cell
The energy can be produced from gas, coal, water but they will not stay for a long time because the energy requirement is increasing day by day. So, IR plastic solar cells are designed with plastic with power enhanced change efficiency. The technology used in this cell is Nano that includes the solar cells which are connected to the IR and invisible rays of the sun.
The working of these cells is similar to conventional solar cells but these are small in size and less weight. The main function of these cells is to change solar energy into electrical in all weather conditions. These cells include nanoparticles namely quantum dots which are united through a polymer for making the plastic to notice the energy in the IR
Paper Battery
The battery that is very thin in size and used as a storage device is known as a paper battery. This battery is very flexible. Please refer to this link to know more about this paper battery, construction, and its working.
A solar tree is one kind of tree that uses solar energy on a single pillar. It is a functional power generator & a solar network. The installation of the solar tree promotes awareness, implementation of renewable energy, and understanding. The structure of the solar tree is like a tree trunk where different modules are placed on a single pillar including an automatic tracking technology.
Generally, they are located on the main roads for power publicity hoardings. These kinds of trees provide awareness & also give shade as well as meeting places.
Electronic Skin
Electronic skin is an artificial skin and it is a very thin electronic device that is attached to the human skin like a tattoo for measuring different parameters of the body like brain signals, heart activity, etc. It is developed in a laboratory & it replaces the skin for people who have suffered from skin shock, skin diseases, and skin burns otherwise robotic applications.
E-Skin is related to the human skin that is embedded through a sense of touch working on the skin. The designing of this can be done using thermostats, electronic measuring devices, pollution detectors, pressure gauges, microphones, cameras, EKGs, glucose sensors, etc.
WSNs can be improved human life in several applications including the capability of environment-sensing like home security, monitoring of buildings, and healthcare. The iMouse system uses a wireless sensor network into surveillance for supporting the services of mobile surveillance.
This can be improved by using two methods; the first method is, to facilitate the navigation of mobile sensors by employing localization methods to direct mobile sensors in place of color tapes whereas the second choice is to develop coordination between mobile sensors, particularly once they are on the highway.
Polymer LED
Polymers are flexible as well as lightweight, used like semiconductors within the LED development. The light-emitting diode which uses polymer is known as polymer LED or Polymer LED. There are different applications of polymer LED like bumpers in automobiles, color display, electronic newspapers, and vests designed like bulletproof, etc.
The list of technical seminar topics on cloud computing includes the following.
Cloud Computing for E-commerce
Cloud computing is used in various sectors like health care, E-learning & E-commerce. It provides online services at less cost with high efficiency to provide high financial worth. In the world of the internet and business, cloud computing is the upcoming revolution. At present, E-commerce companies using Cloud Computing for attaining high practical worth. So cloud computing is very useful in E-commerce.
Agriculture Areas Impact with Cloud Computing
At present, cloud computing is applicable in centralized agricultural-based data bank within the cloud. The development in the latest technology in every field is changed especially in agriculture, cloud computing was affected positively to provide related services for the users.
Security Issues in Cloud Computing
Cloud computing provides computing service through the internet on-demand & disburses for each user to access different resources like storage, services, networks, servers & applications without getting them physically. For organizations, it saves time as well as cost. Generally, data can be stored within relational databases on one otherwise more servers that are placed within the organization & the clients require demanding data from server machines.
Cloud Computing Evolution
While implementing cloud, there are different challenges are faced so, various devices, as well as methods, are established for enhancing the cloud architecture’s performance. The control measures can be applied by the cloud vendors among the services based on cloud & mobile users so that secured service can be provided. FPGA usage can add advantages to cloud computing by providing protected cloud architecture.
The reconfigurable hardware can enhance flexibility, consistency & scalability. The multimedia processing mainly includes difficult operations & computation intensive. So, these applications require an optimized result in terms of power & speed. In cloud computing, the utilization of reconfigurable hardware can enhance the act because of the infrastructure & platform virtualization.
The list of technical seminar topics on artificial intelligence includes the following.
Navigation through Artificial Intelligence
This concept is very useful for disable persons because a disabled person can use his physical movements for navigating around with his intelligence. To overcome this problem, the brain-controlled car is invented. This car works using the artificial intelligence system through different sensors namely monitor of weather, video, anti-collision, etc.
So this car can change the disabled person’s life drastically. Previously, the connection between information theory, neurology & cybernetics can be explored by the researcher in 1940-1950. Some of the researchers designed machines by using the electronic network for displaying rudimentary intelligence.
Artificial Intelligence Impact on Employment
For labor markets, the development in technology & digitalization has main implications. Reviewing its effect will be vital in developing strategies that encourage proficient labor markets for the profit of staff, employers & peoples. So, employment can be threatened by quick progress in technology & innovation. Such a worry is not new but the technology change can cause the loss of jobs. Technology innovation can affect the employee in two main methods like displacement effect and productivity effect.
AI Impact on Management of Complex Projects
The management of complex projects is entering a period of extraordinary challenge & one which deserves further notice and test. This concept mainly focuses on occurs from the improved AI incorporation of all forms like machine learning, AI & processing of natural language into a variety of project implementation elements & the broader corporate structures where these projects exist in.
This project is intended to emphasize the level & width of its growth in the fields of engineering to emphasize the challenges to the business & occupation which should be addressed. The profession of project management would help from learning on the chances and threats that AI will generate.
- Artificial intelligence (AI) in power station
- Artificial intelligence (AI) & Expert Systems
- AI-based Smart Assistants like Alexa & Siri
- Mapping of Disease & Tools for Prediction
- AI in Manufacturing & Drone Robots
- Treatment of Optimized & Personalized Healthcare
- Conversational bots for Customer Service & Marketing
- Robot Advisors for Trading of Stock
- E-mail Spam Filters
- Monitoring Tools for Social Media & False News
- Recommendations for TV/Song from Netflix & Spotify
Technical Seminar Topics on IoT
The list of technical seminar topics based on IoT includes the following.
Monitoring System of Water Quality based on IoT
Previously, water quality can be monitored & tested by using a conventional technique by collecting water samples &send them to the laboratory for testing as well as analysis. But this method takes a lot of time & it is not cheap. To overcome this, the proposed system is implemented for checking the water quality in real-time using different sensors for parameters like conductivity, pH, turbidity, and temperature because of a difference in the parameter value points in the direction of the occurrence of contaminants.
In the system, the Wi-Fi module sends the collected data using sensors toward the microcontroller & sends it to the PC or smartphone. This system checks continuously on the contamination of the water resources & provides protected drinking water.
IoT based Smart Aquaponic System
Getting suitable water resources for farming fish & plants is somewhat difficult. Additionally, the production of agriculture is reducing because of narrower lands so that saving technology for land & water with a range of vegetables is significant to generate the highest yield. The sustainable system for agriculture is Aquaponics by uniting aquaculture & hydroponics. This system must run on the planting medium occasionally to make sure that the plants getting the nutrients whenever the water is filtered correctly through the medium.
So, a smart aquaponics system is developed for monitoring & controlling the amount of acidity, level of water, temperature of water & feed for fish were included through a mobile application based on the internet. In this system, a sensor is used to recover the data which is sent to the IoT Cloud server. Therefore, the circulation of water & quality were well conserved. The final results will show the success rate of different sensors.
Securing IOT Device for Cryptographic Approach
IoT connects different sensing devices to the Internet to exchange data. The IoT shall be capable to include clearly & effortlessly a large number of dissimilar & mixed end systems. Therefore the safety is the most significant thing in this system because this system is very useful in industry, healthcare, etc. This project gives information regarding the safety & cryptographic algorithm that are most suitable for the Internet of Things.
Monitoring System for RO Water using IoT
The most consistent, energy-efficient & cost-effective desalination technology for producing clean water as compared with other technologies is RO (Reverse osmosis). This technology is growing rapidly including a huge number of fittings worldwide. At present, the accessibility of freshwater has been the major factor in the expansion of all peoples.
A key decisive factor of the RO design is the precise electricity utilization, which must be as low as feasible. So, the recovery ratio should be kept high when it is possible & the additional feedwater force must be low when possible, satisfying the drinking water principles & the manufacture’s design guidelines.
The most popular technical seminar topics are listed below. The below-mentioned list of technical seminar topics may help students to select their seminars in the most appropriate way.
1. Mobile train radio communication 2. Paper battery 3. Smart antenna for mobile communication 4. Smart note taker 5. Embedded web technology 6. Low energy efficiency wireless 7. Communication network design 8. Seminar on artificial passenger 9. Blue eyes technology 10. Touch screen technology 11. Traffic pulse technology 12. Pill camera 13. Night vision technology 14. Space mouse 15. Nano-technology 16. Global positioning system and its application 17. Tsunami warning system 18. The smart dust core architecture 19. Advanced technique for RTL 20. Debugging 21. Optical fiber communication 22. Digital image processing 23. Embedded system 24. Electronic watchdog 25. Telephone conversation recorder 26. Aeronautical Communications 27. Agent-oriented programming 28. Air cars 29. Animatronics 30. Artificial Eye 31. Augmented reality 32. Automatic Teller Machine 33. Autonomic Computing 34. BIBS 35. Bi-CMOS technology 36. Bimolecular Computers 37. BIOCHIPS 38. Bio-magnetism 39. Biometric technology 40. BLUE RAY 41. Bluetooth Based Smart Sensor Networks 42. Boiler Instrumentation 43. Brain-Computer Interface 44. Bluetooth technology 45. 3-G Vs Wi-Fi 46. Future generation wireless network 47. Bluetooth-based smart sensor network . 48. White LED 49. Gesture recognition using accelerometer 50. Cellular digital data packet 51. Telecommunication Network PPT 52. Electrical Technical Seminar Topic on CAN-based Higher Layer Protocols and Profiles 53. Application of Swarm Robots 54. Embedded Systems B.tech Final Year Seminar Topic on Smart Phones technology 55. Future Satellite Communication B.tech Seminar Topic 56. 3D image technique and multimedia application 57. Storage area network 58. The making of quantum dots 59. The mp3 standard 60. The Vanadium Redox Flow Battery System 61. Thermal infrared imaging technology 62. Turbo codes 63. Ultra-wideband technology 64. Virtual Reality 65. Voice recognition based on artificial neural networks 66. Web-based remote device monitoring 67. Organic electronics 68. Packet Cable Network 69. Packet Switching chips 70. Personal Area Network 71. Printable RFID circuits 72. Mesh Radio 73. Microelectronic Pills 74. Military Radars 75. Android 76. Control of environment parameter in a greenhouse 77. 3D traditional and modeling 78. Home-based wireless work monitoring system 79. Sun tracker 80. PC interfaced voice recognition system 81. Cybersecurity 82. Big data visualization 83. Interactive public display 84. Next-generation mobile computing 85. Multicore memory coherence 86. Renewable Energy Source Biomass 87. Matter Energy 88. Fusion Technology 89. Electronic Ballast 90. Stepper Motor & its Application 91. Radial Feeder Protection 92. Solar Tower Technology 93. Electric Locomotive 94. Reactive Power Consumption in Transmission Line 95. Flexible A.C. Transmission 96. D.C. Arc Furnace 97. Performance Evaluation & EMI/EMC Testing of Energy Meter 98. Feeder Protective Relay 99. Hydrogen The Future Fuel 100. Quality of electrical power 101. Phase Locked Loop 102. Architecture of an Electric Vehicle 103. 66 K.V. Switch Yards 104. Flexible Photovoltaic Technology 105. DSP For Motor Control 106. Vector control Of Induction Motor 107. Uninterrupted Power Supply 108. Protection of Distribution System 109. Arc Fault Circuit Interrupters 110. 66kv Receiving Sub-Station 111. Nano Fuel Cell 112. Hybrid Electrical Vehicles 113. Relay Performance Testing With High Technology 114. Production of & Protection against Surge 115. HVDC Converter 116. CT scanning 117. Extra high voltage transmission lines 118. Feeder protection 119. Electrical vehicle 120. Energy conversation by soft start 121. Dust collection and scrubbing tech 122. DSP on motor control 123. Earthquake leakage circuit beaker 124. Energy efficient motor 125. Flexi 126. Field oriented control drive without shaft sensors 127. 12 phase capacitor 128. Cable modem 129. Cluster meter system 130. Advancement in inverter technology for industrial application 131. Broadband over power line 132. Development of superconducting rotating machines 133. Direct to home (DTH) 134. E-bomb 135. Smart card technology 136. Fuzzy logic technology 137. MEMS (Micro Electro Mechanical System) 138. Smart material technology 139. Neural networks 140. Simple heat sensor 141. Traffic signal control 142. Electromagnetic bomb 143. E-mail alert system 144. Energy saving fan 145. Electronic fuel injection 146. Direct fuel methanol fuel cell 147. Dual core processor 148. Compensation of harmonic current utilizing AHC 149. AC Cable versus DC Cable Transmission for Offshore Wind Farms 150. Adaptive Piezoelectric Energy Harvesting Circuit 151. Automatic Solar Tracker 152. Artificial Intelligence in Power Station 153. Wireless Power Transmission via Solar Power Satellite 154. Hybrid Electric Vehicle 155. Optical Technology In Current Measurement 156. The Universal Current Sensor 157. Nuclear Batteries 158. Large Scale Power Generation Using Fuel Cell 159. Surge current protection using super conductors 160. Solar Power Generation 161. Buck Boost Transformer 162. Infrared thermograph 163. Digital Testing of High Voltage Circuit Breakers 164. Surge Current Protection Using Super conductors 165. Blue jacking 166. Sixth sense technology 167. 5G mobile technology 168. Nano scale material and device for future communication network 169. Nokia morph technology 170. Confidential data storage and deletion 171. Helio-display 172. Issue of routing IN VANET 173. Touch screen with feelings 174. Femtocells technology 175. Apple- a novel approach for direct energy weapon control 176. Optical Ethernet 177. Transparent electronics 178. Bubble power 179. Hawkeye 180. Data loggers 181. Bluetooth network security 182. Silicon on plastic 183. Human robot interaction 184. Poly fuse 185. Non visible imaging 186. Nuclear battery- daintiest dynamos 187. Mobile IPv6 188. HART communication 189. E-textile 190. FPGA in space 191. Indoor Geo-location 192. Ultra conductors 193. GMPLS 194. SATRACK 195. Multi-sensor fusion and integration 196. Laser communication 197. Iontophoresis 198. Organic display 199. Introduction to internet protocol 200. Cathode ray tube display 201. Global system for mobile communication (GSM) 202. Smart quill 203. Automatic number plate recognition 204. Military radar 205. MIMO wireless channels 206. Telephone router 207. Speed sensor 208. Microcontroller based dissolving process control 209. Local PCO meter 210. Railway switch and signals 211. Card based security system 212. Cordless power controller 213. Weather station 214. Temperature monitoring system
Don’t Miss: Latest Electronics Project Ideas for Engineering Students.
Thus, this is all about the latest technical seminar topics which we have mentioned many interesting seminar topics will be definitely useful for engineering students. So please leave your feedback through the comment section below. We will do our best to reply to your comment as early as possible.
Share This Post:
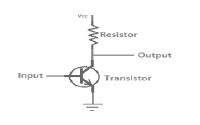
Comments are closed.
- Electronics
- Communication
- Free Circuits
- Interview Questions
- ECE Projects
- EEE Projects
- Project Ideas
- Resistor Color Code Calculator
- Ohms Law Calculator
- Circuit Design
- Infographics

- Most Popular
- Explore all categories
b.tech project report
Engineering.
B.Tech Project Report
Upload: rohit-singh
Post on 21-Nov-2014
2.949 views
17 download
Embed Size (px): 344 x 292 429 x 357 514 x 422 599 x 487
DESCRIPTION

BABU BANARSI DAS INSTITUTE OF TECHNOLOGY, GHAZIABAD
(AFFILIATED TO U.P. TECHNICAL UNIVERSITY, LUCKNOW)
(Established in 2000)
“REAL TIME SPEAKER RECOGNITION”
A project report submitted in partial fulfillment of the requirement for the
Award of Degree of
Bachelor of Technology
Electronics and Communication Engineering
Academic session 2008-2012
Submitted By: Project guides:
Rohit Singh (0803531072) Mr. Prashant Sharma
Harish Kumar (0803531409) Mr. Anil Kumar Pandey
Samreen Zehra (0803531074)
DEPARTMENT OF ELECTRONICS AND COMMUNICATION ENGINEERING

CERTIFICATE
This is to certify that Rohit Singh, Harish Kumar and Samreen Zehra of Department of
Electronics and Communication Engineering of this institute have carried out together the
project work presented in this report entitled „Real Time Speaker Recognition‟ in partial
fulfillment of award of degree of Bachelor of Technology in Electronics and Communication
Engineering from UPTU, Lucknow under our supervision. The report embodies results of
their works and studies carried out by the students themselves and the content of report does
not form the part of any other degree to these candidates or to anybody else.
Project guides:
Mr. Prashant Sharma (AP, ECE)
Mr. Anil Kumar Pandey (AP, ECE)

ACKNOWLEDGEMENT
We have taken efforts in this project. However, it would not have been possible without the
kind support and help of many individuals. We would like to extend our sincere thanks to all
We are highly indebted to Mr. K. L. Pursnani, Head of Department Electronic and
Communication Engineering, BBDIT, Ghaziabad, for his guidance and constant supervision
as well as for providing necessary information regarding the project & for his support in
completing the project.
We would like to express our special gratitude and thanks to our project guides, Mr. Prashant
Sharma and Mr. Anil Kumar Pandey for giving us such attention and time. Both of our guides
had taken great pain and efforts to help us the best way without whom this project would ever
be realized.
We would like to express our gratitude towards our parents and friends for their kind co-
operation and encouragement which help us in completion of this project.
Our thanks and appreciations also go to our college in developing the project and people who
have willingly helped us out with their abilities.
Rohit Singh (0803531072)
Harish Kumar (0803531409)

1. Introduction…………………………………………………………………………...7
1.1 Project overview……………………………..…………………....………..……..7
1.2 Application…………………...………………………………...………………...10
2. Methodology……………...………………………………………….………………11
2.1 Algorithm………………………………………………...………………………11
2.2 Flow Chart……………………………………………...………………………...12
3. Identification background……………………………………………………….….13
3.1 DSP Fundamentals………………………………………………...……………..13
3.1.1 Basic Definitions………...………………………………….………...…..13
3.1.2 Convolution………………………………………………..……………...14
3.1.3 Discrete Fourier Transform………………………………...……………..14
3.2 Human Speech Production Model…………………………………...…………...15
3.2.1 Anatomy..………………………………………………….……………...15
3.2.2 Vocal Model……………………………………….…………………..….17
3.3 Speaker Identification……………………………………...……………………..18
4. Speech Feature Extraction……………………………………………………….…21
4.1 Introduction…………………………………………………………………...…..21
4.2 Short term analysis…..……………………………………………...…………....22
4.3 Cepstrum…………………………………………………………………...…….23
4.3.1 Delta Cepstrum……………..……………………………………….……24
4.4 Mel-Frequency Cepstrum Coefficients……………………………………….......25
4.4.1 Computing of mel cepstrum coefficient……………………………..……27
4.5 Framing and Windowing………..............................................................................29
5. Vector Quantization……………………………………………..………………......30
6. K-means………………………………………………………………………….…..33
6.1 Mean shift clustering…….…………………………………………...……...…...35
6.2 Bilateral filtering…….………………………………………………………........36
6.3 Speaker matching…………………..……………………………………..……….36
7. Euclidean distance………………………………………………………………...…...38
7.1 One dimension…………………………………………………………...……….40
7.2 Two dimension…………………….…………………………………..…………40

7.3Three dimension………….………………………………………………………..40
7.4 N dimensions………………………………………………………………….......40
7.5 Squared euclidean distance …………………....……………………...………….40
7.6 Decision making……………………………………………………...…………..41
8 Result and Conclusion…………………………………………………………………..42
8.1 Result…………………………………………………………………………......42
8.2 Pruning Basis…………………...…………………………………………...…...42
8.2.1 Static Pruning…………………………………………………………43
8.2.2 Adaptive Pruning……………………………………………………..44
8.3 Conclusion…………………………………………………………….....……….44

LIST OF FIGURES
Name of Figure Page No
1.1 Identification Taxonomy………………………………………………………………..….8
3.1 Vocal Tract Model…………………………………………………………………….….16
3.2 Multi tube Lossless Model…………………...…………………………………..……….17
3.3 Source Filter Model……………………………………….………………….…………..18
3.4 Enrollment Phase…………………………………………………………….…………...19
3.5 Identification Phase………………………………………………………..……………...20
4.1 Short Term Analysis……………………………………………………….……………..23
4.2 Speech Magnitude Spectrum…………………………………………….……………….25
4.3 Cepstrum………………………………………………………………………….………25
4.4 Computing of mel-cepstrum coefficient……………………………………….…………27
4.5 Triangular Filter used to compute mel-cepstrum ………………………………..……….28
4.6 Quasi Stationary………………………………………………………………..…………29
5.1 Vector Quantization of Two Speakers………………………………………..…………..31
7.1 Decision Process…………………………………………………………….……………41
8.1 Distance stabilization……………………………………………………….…………….42
8.2 Evaluation of static variant using different pruning intervals…………………..………...43
8.3 Examples of the matching score distribution………………………………..……………44

INTRODUCTION
1.1 Project overview
The human speech conveys different types of information. The primary type is the meaning or
words, which speaker tries to pass to the listener. But the other types that are also included in
the speech are information about language being spoken, speaker emotions, gender and
identity of the speaker. The goal of automatic speaker recognition is to extract, characterize
and recognize the information about speaker identity. Speaker recognition is usually divided
into two different branches:
Speaker verification
Speaker identification.
Speaker verification task is to verify the claimed identity of person from his voice. This
process involves only binary decision about claimed identity. In speaker identification there is
no identity claim and the system decides who the speaking person is.
Speaker identification can be further divided into two branches. Open-set speaker
identification decides to whom of the registered speakers‟ unknown speech sample belongs or
makes a conclusion that the speech sample is unknown. In this work,
we deal with the closed-set speaker identification, which is a decision making process of who
of the registered speakers is most likely the author of the unknown speech sample. Depending
on the algorithm used for the identification, the task can also be divided into text-dependent
and text-independent identification. The difference is that in the first case the system knows
the text spoken by the person while in the second case the system must be able to recognize
the speaker from any text. This taxonomy is
Represented in Figure 1.1

Speaker Recognition
Speaker verification Speaker identification
Closed set Identification Open set Identification
Text independent identification Text dependent identification
Fig. 1.1 Identification Taxonomy
Speaker recognition is basically divided into two-classification: speaker recognition and
speaker identification and it is the method of automatically identify who is speaking on the
basis of individual information integrated in speech waves. Speaker recognition is widely
applicable in use of speaker‟s voice to verify their identity and control access to services such
as banking by telephone, database access services, voice dialing telephone shopping,
information services, voice mail, security control for secret information areas, and remote
access to computer AT and T and TI with Sprint have started field tests and actual
application of speaker recognition technology; many customers are already being used by
Sprint‟s Voice Phone Card.

Speaker recognition technology is the most potential technology to create new services that
will make our everyday lives more secured. Another important application of speaker
recognition technology is for forensic purposes. Speaker recognition has been seen an
appealing research field for the last decades which still yields a number of unsolved problems.
The main aim of this project is speaker identification, which consists of comparing a speech
signal from an unknown speaker to a database of known speaker. The system can recognize
the speaker, which has been trained with a number of speakers. Below figure shows the
fundamental formation of speaker identification and verification systems. Where the speaker
identification is the process of determining which registered speaker provides a given
speech. On the other hand, speaker verification is the process of rejecting or accepting the
identity claim of a speaker. In most of the applications, voice is use as the key to confirm the
identities of a speaker is classified as speaker verification.
Adding the open set identification case in which a reference model for an unknown speaker
may not exist can also modify above formation of speaker identification and verification
system. This is usually the case in forensic application. In this circumstances, an added
decision alternative, the unknown does not match any of the models, is required. Other
threshold examination can be used in both verification and identification process to decide
if the match is close enough to acknowledge the decision or if more speech data are
Speaker recognition can also divide into two methods, text-dependent and text independent
methods. In text dependent method the speaker has to say key words or sentences having the
same text for both training and recognition trials. Whereas in the text independent does not
rely on a specific text being speaks. Formerly text dependent methods were widely in
application, but later text independent is in use. Both text dependent and text independent
methods share a problem however.
By playing back the recorded voice of registered speakers this system can be easily deceived.
There are different technique is used to cope up with such problems. Such as a small set of
words or digits are used as input and each user is provoked to thorough a specified
sequence of key words that is randomly selected every time the system is used. Still this
method is not completely reliable. This method can be deceived with the highly developed
electronics recording system that can repeat secrete key words in a request order. Practical

applications for automatic speaker identification are obviously various kinds of security
systems. Human voice can serve as a key for any security objects, and it is not so easy in
general to lose or forget it. Another important property of speech is that it can be transmitted
by telephone channel, for example. This provides an ability to automatically identify speakers
and provide access to security objects by telephone. Nowadays, this approach begins to be
used for telephone credit card purchases and bank transactions. Human voice can also be used
to prove identity during access to any physical facilities by storing speaker model in a small
chip, which can be used as an access tag, and used instead of a pin code. Another important
application for speaker identification is to monitor people by their voices. For instance, it is
useful in information retrieval by speaker indexing of some recorded debates or news, and
then retrieving speech only for interesting speakers. It can also be used to monitor criminals in
common places by identifying them by voices. In fact, all these examples are actually
examples of real time systems. For any identification system to be useful in practice, the time
response, or time spent on the identification should be minimized. Growing size of speaker
database is its major limitation.
1.2 Application
Practical applications for automatic speaker identification are obviously various kinds of
security systems. Human voice can serve as a key for any security objects, and it is not so
easy in general to lose or forget it. Another important property of speech is that it can be
transmitted by telephone channel, for example. This provides an ability to automatically
identify speakers and provide access to security objects by telephone. Nowadays, this
approach begins to be used for telephone credit card purchases and bank transactions. Human
voice can also be used to prove identity during access to any physical facilities by storing
speaker model in a small chip, which can be used as an access tag, and used instead of a pin
code. Another important application for speaker identification is to monitor people by their
voices. For instance, it is useful in information retrieval by speaker indexing of some recorded
debates or news, and then retrieving speech only for interesting speakers. It can also be used
to monitor criminals in common places by identifying them by voices.
In fact, all these examples are actually examples of real time systems. For any identification
system to be useful in practice, the time response, or time spent on the identification should be
minimized. Growing size of speaker database is its major limitation.

METHODOLOGY
2.1 Algorithm
1. Record the test sound through microphone.
2. Convert the recorded sound into .wav format.
3. Load recorded sound files from database.
4. Extract features from test file for recognition.
5. Extract features from all the files stored in the database.
6. Find out the centroids of the test file by any clustering algorithm.
7. Find out the centroids of the sample files stored in database so that codebooks can be
8. Calculate the Euclidean distance between the test file and individual samples of the
9. Find out the sample having minimum distance with the test file.
10. The sample corresponding to the minimum distance is most likely the author of the test

2.2 Flowchart

IDENTIFICATION BACKGROUND
In this chapter we discuss theoretical background for speaker identification. We start from the
digital signal processing theory. Then we move to the anatomy of human voice production
organs and discuss the basic properties of the human speech production mechanism and
techniques for its modeling. This model will be used in the next chapter when we will discuss
techniques for the extraction of the speaker characteristics from the speech signal.
3.1 DSP Fundamentals
According to its abbreviation, Digital Signal Processing (DSP) is a part of computer science,
which operates with special kind of data – signals. In most cases, these signals are obtained
from various sensors, such as microphone or camera. DSP is the mathematics, mixed with the
algorithms and special techniques used to manipulate with these signals, converted to the
digital form.
3.1.1 Basic Definitions
By signal we mean here a relation of how one parameter is related to another parameter. One
of these parameters is called independent parameter (usually it is time), and the other one is
called dependent, and represents what we are measuring. Since both of these parameters
belong to the continuous range of values, we call such signal continuous signal. When
continuous signal is passed through an Analog-To-Digital converter (ADC)it is said to be
discrete or digitized signal. Conversion works in the following way: every time period, which
occurs with frequency, called sampling frequency, signal value is taken and quantized, by
selecting an appropriate value from the range of7possible values. This range is called
quantization precision and usually represented as an amount of bits available to store signal
value. Based on the sampling theorem, proved by Nyquist in 1940, digital signal can contain
frequency components only up to one half of the sampling rate. Generally, continuous signals
are what we have in nature while discrete signals exist mostly inside computers. Signals that
use time as the independent parameter are said to be in the time domain, while signals that use

frequency as the independent parameter are said to be in the frequency domain. One of the
important definitions used in DSP is the definition of linear system. By system we mean here
any process that produces output signal in response on a given input signal. A system is called
linear if it satisfies the following three properties: homogeneity, additivity and shift
invariance.
3.1.2 Convolution
An impulse is a signal composed of all zeros except one non-zero point. Every signal can be
decomposed into a group of impulses, each of them then passed through a linear system and
the resulting output components are synthesized or added together. The resulting signal is
exactly the same as obtained by passing the original signal through the system. Every impulse
can be represented as a shifted and scaled delta function, which is a normalized impulse, that
is, sample number zero has a value of one and all other samples have a value of zero. When
the delta function is passed through a linear system, its output is called impulse response. If
two systems are different they will have different impulse responses. Scaled and shifted
impulse response and scaling and shifting of the input are identical to the scaling and shifting
of the output. It means that knowing systems impulse response we know everything about the
system. Convolution is a formal mathematical operation, which is used to describe
Relationship between three signals of interest: input and output signals, and the impulse
response of the system. It is usually said that the output signal is the input signal convolved
with the system‟s impulse response. Mathematics behind the convolution does not restrict
how long the impulse response is. It only says that the size of the output signal is the size of
the input signal plus the size of the impulse response minus one. Convolution is very
important concept in DSP. Based on the properties of linear systems it provides the way of
combining two signals to form a third signal. A lot of mathematics behind the DSP is based
on the convolution.
3.1.3 Discrete Fourier Transform
Fourier transform belongs to the family of linear transforms widely used in DSP based on
decomposing signal into sinusoids (sine and cosine waves).Usually in DSP we use the
Discrete Fourier Transform (DFT), a special kind of Fourier transform used to deal with a
periodic discrete signals. Actually there are an infinite number of ways how signal can be

decomposed but sinusoids are selected because of their sinusoidal fidelity that means that
sinusoidal input to the linear system will produce sinusoidal output, only the amplitude and
phase may change, frequency and shape remain the same.
3.2 Human Speech Production Model
Undoubtedly, ability to speak is the most important way for humans to communicate between
each other. Speech conveys various kind of information, which is essentially the meaning of
information speaking person wants to impart, individual information representing speaker and
also some emotional filling. Speech production begins with the initial formalization of the
idea which speaker wants to impart to the listener. Then speaker converts this idea into the
appropriate order of words and phrases according to the language. Finally, his brain produces
motor nerve commands, which move the vocal organs in an appropriate way. Understanding
of how human produce sounds forms the basis of speaker identification.
3.2.1 Anatomy
The sound is an acoustic pressure formed of compressions and rarefactions of air molecules
that originate from movements of human anatomical structures. Most important components
of the human speech production system are the lungs (source of air during speech), trachea
(windpipe), larynx or its most important part vocal cords (organ of voice production), nasal
cavity (nose), soft palate or velum (allows passage of air through the nasal cavity), hard
palate (enables consonant articulation), tongue, teeth and lips. All these components, called
articulators by speech scientists, move to different positions to produce various sounds. Based
on their production, speech sounds can also be divided into consonants and voiced and
unvoiced vowels.
From the technical point of view, it is more useful to think about speech production system in
terms of acoustic filtering operations that affect the air going from the lungs. There are three
main cavities that comprise the main acoustic filter. According to they are nasal, oral and
pharyngeal cavities.
The articulators are responsible for changing the properties of the system and form its output.
Combination of these cavities and articulators is called vocal tract. Its simplified acoustic

model is represented in Figure 3.1.
Fig. 3.1 Vocal Tract Model
Speech production can be divided into three stages: first stage is the sound source production,
second stage is the articulation by vocal tract, and the third stage is sound radiation or
propagation from the lips and/or nostrils. A voiced sound is generated by vibratory motion of
the vocal cords powered by the airflow generated by expiration. The frequency of oscillation
of vocal cords is called the fundamental frequency. Another type of sounds -unvoiced sound
is produced by turbulent airflow passing through a narrow constriction in the vocal tract.
In a speaker recognition task, we are interested in the physical properties of human vocal
tract. In general it is assumed that vocal tract carries most of the speaker related information.
However, all parts of human vocal tract described above can serve as speaker dependent
characteristics. Starting from the size and power of lungs, length and flexibility of trachea and
ending by the size, shape and other physical characteristics of tongue, teeth and lips. Such
characteristics are called physical distinguishing factors. Another aspects of speech
production that could be useful indiscriminating between speakers are called learned factors,
which includes peaking rate, dialect, and prosodic effects.

3.2.2 Vocal Model
In order to develop an automatic speaker identification system, we should construct
reasonable model of human speech production system. Having such a model, we can extract
its properties from the signal and, using them, we can decide whether or not two signals
belong to the same model and as a result to the same speaker.
Modeling process is usually divided into two parts: the excitation (or source) modeling and
the vocal tract modeling. This approach is based on the assumption of independence of the
source and the vocal tract models. Let us look first at the continuous-time vocal tract model
called multi tube lossless model, which is based on the fact that production of speech is
characterized by changing the vocal tract shape. Because the formalization of such a time-
varying vocal-tract shape model is quite complex, in practice it is simplified to the series of
concatenated lossless acoustic tubes with varying cross-sectional areas, as shown in Figure.
This model consists of a sequence of tubes with cross-sectional areas Ak and lengths Lk. In
practice the lengths of tubes assumed to be equal. If a large amount of short tubes is used,
then we can approach to the continuously varying cross-sectional area, but at the cost of more
complex model. Tract model serves as a transition to the more general discrete-time model,
also known as source-filter model, which is shown in Figure.
Fig. 3.2 Multi tube Lossless Model

In this model, the voice source is either a periodic pulse stream or uncorrelated white noise, or
a combination of these. This assumption is based on the evidence from human anatomy that
all types of sounds, which can be produced by humans, are divided into three general
categories: voiced, unvoiced and combination of these two. Voiced signals can be modeled as
a basic or fundamental frequency signal filtered by the vocal tract and unvoiced as a white
noise also filtered by the vocal tract. Here E(z) represents the excitation function, H(z)
represents the transfer function, ands(n) is the output of the whole speech production system
[8]. Finally, we can think about vocal tract as a digital filter, which affects source signal and
about produced sound output as a filter output. Then based on the digital filter theory we can
extract the parameters of the system from its output
Fig.3.3 Source Filter Model
3.3 Speaker Identification
into two different branches, speaker verification and speaker identification. Speaker
verification task is to verify the claimed identity of person from his voice. This process
involves only binary decision about claimed identity. In speaker identification there is no
identity claim and the system decides who the speaking person is Speaker identification can

be further divided into two branches. Open-set speaker identification decides to whom of the
registered speakers‟ unknown speech sample belongs or makes a conclusion that the speech
sample is unknown. In this work, we deal with the closed-set speaker identification, which is
a decision making process of whom of the registered speakers is most likely the author of the
unknown speech sample. Depending on the algorithm used for the identification, the task can
also be divided into text-dependent and text-independent identification. The difference is that
in the first case the system knows the text spoken by the person while in the second case the
system must be able to recognize the speaker from any text.
The process of speaker identification is divided into two main phases.
1) Speaker enrollment
2) Speaker Identification
During the first phase, speaker enrollment, speech samples are collected from
The speakers and they are used to train their models. The collection of enrolled models is also
called a speaker database. Then in the enrollment phase, these features are modeled and stored
in the speaker database. This process is represented in following figure.
Fig. 3.4 Enrollment Phase
The next phase of speech recognition is identification phase which is shown below in the
figure. In the second phase, identification phase, a test sample from an unknown speaker is
compared against the speaker database. Both phases include the same first step, Feature
extraction, which is used to extract speaker dependent characteristics from speech. The main
purpose of this step is to reduce the amount of test data while retaining speaker discriminative
information.

Fig. 3.5 Identification Phase
However, these two phases are closely related. For instance, identification algorithm usually
depends on the modeling algorithm used in the enrollment phase. This thesis mostly
concentrates on the algorithms in the identification phase and their optimization.

SPEECH FEATURE EXTRACTION
4.1 Introduction
The acoustic speech signal contains different kind of information about speaker. This includes
“high-level” properties such as dialect, context, speaking style, emotional state of speaker and
many others. A great amount of work has been already done in trying to develop
identification algorithms based on the methods used by humans to identify speaker. But these
efforts are mostly impractical because of their complexity and difficulty in measuring the
speaker discriminative properties used by humans. More useful approach is based on the
“low-level” properties of the speech signal such as pitch (fundamental frequency of the vocal
cord vibrations), intensity, formant frequencies and their bandwidths, spectral correlations,
short-time spectrum and others. From the automatic speaker recognition task point of view, it
is useful to think about speech signal as a sequence of features that characterize both the
speaker as well as the speech. It is an important step in recognition process to extract
sufficient information for good discrimination in a form and size which is amenable for
effective modeling. The amount of data, generated during the speech production, is quite large
while the essential characteristics of the speech process change relatively slowly and
therefore, they require less data.
According to these matters feature extraction is a process of reducing data while retaining
speaker discriminative information.
When dealing with speech signals there are some criteria that the extracted features should
meet. Some of them are listed below:
discriminate between speakers while being tolerant of intra-speaker variability,
easy to measure,
stable over time,
occur naturally and frequently in speech,
change little from one speaking environment to another,
Not be susceptible to mimicry.

For MFCC feature extraction, we use the melcepst function from Voicebox. Because of its
nature, the speech signal is a slowly varying signal or quasi-stationary. It means that when
speech is examined over a sufficiently short period of time (20-30 milliseconds) it has quite
stable acoustic characteristics. It leads to the useful concept of describing human speech
signal, called “short-term analysis”, where only a portion of the signal is used to extract signal
features at one time. It works in the following way: predefined length window (usually 20-30
milliseconds) is moved along the signal with an overlapping (usually 30-50% of the window
length) between the adjacent frames. Overlapping is needed to avoid losing of information.
Parts of the signal formed in such a way are called frames. In order to prevent an abrupt
change at the end points of the frame, it is usually multiplied by a window function. The
operation of dividing signal into short intervals is called windowing and such segments are
called windowed frames (or sometime just frames). There are several window functions used
in speaker recognition area but the most popular is Hamming window function, which is
described by the following equation:
𝑊 𝑛 = 0.54− 0.46cos(2𝑛𝜋
Where N is the size of the window or frame. A set of features extracted from one frame is
called feature vector.
4.2 Short Term Analysis
Frame1, Frame2, Frame3, … Frame N the speech signal is slowly varying over time (quasi-
stationary), that is when the signal is examined over a short period of time (5-100msec), the
signal is fairly stationary. Therefore speech signals are often analyzed in short time segments,
which is referred to as short-time spectral analysis.

Fig. 4.1 Short Term Analysis
4.3 Cepstrum
The speech signal s(n) can be represented as a “quickly varying” source signal e(n)
convolved with the “slowly varying” impulse response h(n) of the vocal tract represented as a
linear filter. We have access only to the output (speech signal) and it is often desirable to
eliminate one of the components. Separation of the source and the filter parameters from the
mixed output is in general difficult problem when these components are combined using not
linear operation, but there are various techniques appropriate for components combined
linearly. The cepstrum is representation of the signal where these two components are
resolved into two additive parts. It is computed by taking the inverse DFT of the logarithm of
the magnitude spectrum of the frame. This is represented in the following equation:

𝐶𝑒𝑝𝑠𝑡𝑟𝑢𝑚 𝑓𝑟𝑎𝑚𝑒 = 𝐼𝐷𝐹𝑇 log 𝐷𝐹𝑇 𝑓𝑟𝑎𝑚𝑒
Some explanation of the algorithm is therefore needed. By moving to the frequency domain
we are changing from the convolution to the multiplication. Then by taking logarithm we are
moving from the multiplication to the addition. That is desired division into additive
components. Then we can apply linear operator inverse DFT, knowing that the transform will
operate individually on these two parts and knowing what Fourier transform will do with
quickly varying and slowly varying parts. Namely it will put them into different, hopefully
separate parts in new, also called quefrency axis.
4.3.1 Delta Cepstrum
The cepstral coefficients provide a good representation of the local spectral properties
of the framed speech. But, it is well known that a large amount of information resides
in the transitions from one segment of speech to another. An improved representation can
be obtained by extending the analysis to include information about the temporal cepstral
derivative. Delta Cepstrum is used to catch the changes between the different frames. Delta
Cepstrum defined as:
2{𝐶𝑠 𝑛;𝑚 + 1 − 𝐶𝑠(𝑛;𝑚 − 1)}
The results of the feature extraction are a series of vectors characteristic of the time-
varying spectral properties of the speech signal.

Fig.4.2 Speech Magnitude Spectrum
We can see that the speech magnitude spectrum is combined from slow and quickly varying
parts. But there is still one problem: multiplication is not a linear operation. We can solve it
by taking logarithm from the multiplication as described earlier. Finally, let us look at the
result of the inverse DFT in Figure.
Fig.4.3Cepstrum
We can see that two components are clearly distinctive now.
4.4 Mel-Frequency Cepstrum Coefficients
In this project we are using Mel Frequency Cepstral Coefficient. Mel frequency Cepstral
Coefficients are coefficients that represent audio based on perception. This coefficient has a
great success in speaker recognition application. It is derived from the Fourier Transform of
the audio clip. In this technique the frequency bands are positioned logarithmically, whereas
in the Fourier Transform the frequency bands are not positioned logarithmically. As the
frequency bands are positioned logarithmically in MFCC, it approximates the human

system response more closely than any other system. These coefficients allow better
processing of data. In the Mel Frequency Cepstral Coefficients the calculation of the Mel
Cepstrum is same as the real Cepstrum except the Mel Cepstrum‟s frequency scale is warped
to keep up a correspondence to the Mel scale. The Mel scale was projected by Stevens,
Volkmann and Newman in 1937. The Mel scale is mainly based on the study of observing the
pitch or frequency Perceived by the human. The scale is divided into the units mel. In this test
the listener or test person started out hearing a frequency of 1000 Hz, and labeled it 1000 Mel
for reference. Then the listeners were asked to change the frequency till it reaches to the
frequency twice the reference frequency. Then this frequency labeled 2000 Mel. The same
procedure repeated for the half the frequency, then this frequency labeled as 500 Mel, and so
on. On this basis the normal frequency is mapped into the Mel frequency. The Mel scale is
normally a linear mapping below 1000 Hz and logarithmically spaced above 1000 Hz. Figure
below shows the example of normal frequency is mapped into the Mel frequency.
Mel-frequency cepstrum coefficients (MFCC) are well known features used to describe
speech signal. They are based on the known evidence that the information carried by low-
frequency components of the speech signal is phonetically more important for humans than
carried by high-frequency components. Technique of computing MFCC is based on the short-
term analysis, and thus from each frame a MFCC vector is computed. MFCC extraction is
similar to the cepstrum calculation except that one special step is inserted, namely the
frequency axis is warped according to the mel-scale. Summing up, the process of extracting
MFCC from continuous speech is illustrated in Figure.
A “mel” is a unit of special measure or scale of perceived pitch of a tone. It does not
correspond linearly to the normal frequency, indeed it is approximately linear below 1 kHz
and logarithmic above.

4.4.1Computing of melcepstrum coefficients
Fig. 4.4 Computing of mel-cepstrum coefficient
Figure above shows the calculation of the Mel Cepstrum Coefficients. Here we are using the
bank filter to warping the Mel frequency. Utilizing the bank filter is much more convenient to
do Mel frequency warping, with filters centered according to Mel frequency. According to the
Mel frequency the width of the triangular filters vary and so the log total energy in a critical
band around the center frequency is included. After warping are a number of coefficients.
Finally we are using the Inverse Discrete Fourier Transformer for the cepstral coefficients
calculation. In this step we are transforming the log of the quefrench domain coefficients to
the frequency domain. Where N is the length of the DFT we used in the cepstrum section.
To place more emphasize on the low frequencies one special step before inverse DFT in
calculation of cepstrum is inserted, namely mel-scaling. A “mel” is a unit of special measure
or scale of perceived pitch of a tone. It does not correspond linearly to the normal frequency,
indeed it is approximately linear below 1 kHz and logarithmic above. This approach is based
on the psychophysical studies of human perception of the frequency content of sounds. One

useful way to create mel-spectrum is to use a filter bank, one filter for each desired mel-
frequency component. Every filter in this bank has triangular band pass frequency response.
Such filters compute the average spectrum around each center frequency with increasing
bandwidths, as displayed in Figure.
Fig. 4.5 Triangular Filter used to compute mel-cepstrum
This filter bank is applied in frequency domain and therefore, it simply amounts to taking
these triangular filters on the spectrum. In practice the last step of taking inverse DFT is
replaced by taking discrete cosine transform(DCT) for computational efficiency.
The number of resulting mel-frequency cepstrum coefficients is practically chosen relatively
low, in the order of 12 to 20 coefficients. The zeroth coefficient is usually dropped out
because it represents the average log-energy of the frame and carries only a little speaker
specific information.
However, MFCC are not equally important in speaker identification and thus some
coefficients weighting might by applied to acquire more precise result. Different approach to
the computation of MFCC than described in this work is represented in that is simplified by
omitting filter bank analysis.

4.5 Framing and Windowing
The speech signal is slowly varying over time (quasi-stationary) that is when the signal is
examined over a short period of time (5-100msec), the signal is fairly stationary. Therefore
speech signals are often analyzed in short time segments, which are referred to as
short-time spectral analysis. This practically means that the signal is blocked in frames
of typically 20-30 msec. Adjacent frames typically overlap each other with 30-50%,
this is done in order not to lose any information due to the windowing.
Fig 4.6 Quasi Stationary
After the signal has been framed, each frame is multiplied with a window function w(n) with
length N, where N is the length of the frame. Typically the Hamming window is used:
𝑊 𝑛 = 0.54− 0.46cos(2𝜋𝑛
Where 0 ≤ 𝑛 ≤ 𝑁 − 1
The windowing is done to avoid problems due to truncation of the signal as windowing helps
in the smoothing of the signal.

VECTOR QUANTIONZATION
A speaker recognition system must able to estimate probability distributions of the
computed feature vectors. Storing every single vector that generate from the training mode
is impossible, since these distributions are defined over a high-dimensional space. It is
often easier to start by quantizing each feature vector to one of a relatively small number of
template vectors, with a process called vector quantization. VQ is a process of taking a large
set of feature vectors and producing a smaller set of measure vectors that represents the
centroids of the distribution.
The technique of VQ consists of extracting a small number of representative feature vectors
as an efficient means of characterizing the speaker specific features. By means of VQ, storing
every single vector that we generate from the training is impossible.
Vector quantization (VQ) is a process of mapping vectors from a vector space to a finite
number of regions in that space. These regions are called clusters and represented by their
central vectors or centroids. A set of centroids, which represents the whole vector space, is
called a codebook. In speaker identification, VQ is applied on the set of feature vectors
extracted from the speech sample and as a result, the speaker codebook is generated. Such
codebook has a significantly smaller size than extracted vector set and referred as a speaker
Actually, there is some disagreement in the literature about approach used in VQ. Some
authors consider it as a template matching approach because VQ ignores all temporal
variations and simply uses global averages (centroids). Other authors consider it as a
stochastic or probabilistic method, because VQ uses centroids to estimate the modes of a
probability distribution. Theoretically it is possible that every cluster, defined by its centroid,
models particular component of the speech. But practically, however, VQ creates
unrealistically clusters with rigid boundaries in a sense that every vector belongs to one and
only one cluster. Mathematically a VQ task is defined as follows: given a set of feature
vectors, find a partitioning of the feature vector space into the predefined number of regions,
which do not overlap with each other and added together form the whole feature vector space.
Every vector inside such region is represented by the corresponding centroid. The process of
VQ for two speakers is represented in Figure.

Fig. 5.1 Vector Quantization of Two Speakers
There are two important design issues in VQ: the method for generating the codebook and
codebook size. Known clustering algorithms for codebook generation are:
Generalized Lloyd algorithm (GLA),
Self-organizing maps (SOM),
Pair wise nearest neighbor (PNN),
Iterative splitting technique (SPLIT),
Randomized local search (RLS).
According to, iterative splitting technique should be used when the running time is important
but RLS is simpler to implement and generates better codebooks in the case of speaker

identification task. Codebook size is a trade-off between running time and identification
accuracy. With large size, identification accuracy is high but at the cost of running time and
vice versa. Experimental result obtained in is that saturation point choice is 64 vectors in
codebook. The quantization distortion (quality of quantization) is usually computed as the
sum of squared distances between vector and its representative (centroid). The well-known
distance measures are Euclidean, city block distance.

The K-means algorithm partitions the T feature vectors into M centroids. The algorithm first
chooses M cluster-centroids among the T feature vectors. Then each feature vector is assigned
to the nearest centroid, and the new centroids are calculated. This procedure is continued until
a stopping criterion is met, that is the mean square error between the feature vectors and the
cluster-centroids is below a certain threshold or there is no more change in the cluster-center
assignment.
In data mining, k-means clustering is a method of cluster analysis which aims
to partition n observations into k clusters in which each observation belongs to the cluster
with the nearest mean. This results into a partitioning of the data space into cells. The problem
is computationally difficult (NP-hard), however there are efficient heuristic algorithms that
are commonly employed and converge fast to a local optimum. These are usually similar to
the expectation-maximization algorithm for mixtures of Gaussian distributions via an iterative
refinement approach employed by both algorithms. Additionally, they both use cluster centers
to model the data, however k-means clustering tends to find clusters of comparable spatial
extent, while the expectation-maximization mechanism allows clusters to have different
The most common algorithm uses an iterative refinement technique. Due to its ubiquity it is
often called the k-means algorithm; it is also referred to as Lloyd's algorithm, particularly in
the computer science community.
Given an initial set of k means m1(1)
(see below), the algorithm proceeds by
alternating between two steps:

Where each 𝑥𝑝 goes into exactly one 𝑆𝑖(𝑡)
, even if it could go in two of them. Update step:
Calculate the new means to be the centroid of the observations in the cluster.
The algorithm is deemed to have converged when the assignments no longer change.
Commonly used initialization methods are Forgy and Random Partition. The Forgy method
randomly chooses k observations from the data set and uses these as the initial means. The
Random Partition method first randomly assigns a cluster to each observation and then
proceeds to the Update step, thus computing the initial means to be the centroid of the
cluster's randomly assigned points. The Forgy method tends to spread the initial means out,
while Random Partition places all of them close to the center of the data set. According to
Hamerly et al., the Random Partition method is generally preferable for algorithms such as the
k-harmonic means and fuzzy k-means. For expectation maximization and standard k-means
algorithms, the Forgy method of initialization is preferable.
Given a set of observations (x1, x2, …, xn), where each observation is a d-dimensional real
vector, k-means clustering aims to partition the n observations into k sets
(k ≤ n) S = {S1, S2, …, Sk} so as to minimize the within-cluster sum of squares (WCSS):
Where μi is the mean of points in Si.
The two key features of k-means which make it efficient are often regarded as its biggest
Euclidean distance is used as a metric and variance is used as a measure of cluster scatter.
The number of clusters k is an input parameter: an inappropriate choice of k may yield
poor results. That is why, when performing k-means, it is important to run diagnostic
checks for determining the number of clusters in the data set.
A key limitation of k-means is its cluster model. The concept is based on spherical clusters
that are separable in a way so that the mean value converges towards the cluster center. The
clusters are expected to be of similar size, so that the assignment to the nearest cluster center

is the correct assignment. When for example applying k-means with a value of onto
the well-known Iris flower data set, the result often fails to separate the three Iris species
contained in the data set. With , the two visible clusters (one containing two species)
will be discovered, whereas with one of the two clusters will be split into two even
parts. In fact, is more appropriate for this data set, despite the data set containing
3 classes. As with any other clustering algorithm, the k-means result relies on the data set to
satisfy the assumptions made by the clustering algorithms. It works very well on some data
sets, while failing miserably on others.
The result of k-means can also be seen as the Voronoi cells of the cluster means. Since data is
split halfway between cluster means, this can lead to suboptimal splits as can be seen in the
"mouse" example. The Gaussian models used by the Expectation-maximization
algorithm (which can be seen as a generalization of k-means) are more flexible here by having
both variances and covariance. The EM result is thus able to accommodate clusters of variable
size much better than k-means as well as correlated cluster.
k-means clustering in particular when using heuristics such as Lloyd's algorithm is rather easy
to implement and apply even on large data sets. As such, it has been successfully used in
various topics, ranging from market segmentation, computer vision, geostatistics
and astronomy to agriculture. It often is used as a preprocessing step for other algorithms, for
example to find a starting configuration.
k-means clustering, and its associated expectation-maximization algorithm, is a special case of
a Gaussian mixture model, specifically, the limit of taking all covariance as diagonal, equal,
and small. It is often easy to generalize a k-means problem into a Gaussian mixture model.
6.1Mean shift clustering
Basic mean shift clustering algorithms maintain a set of data points the same size as the input
data set. Initially, this set is copied from the input set. Then this set is iteratively replaced by
the mean of those points in the set that are within a given distance of that point. By
contrast, k-means restricts this updated set to k points usually much less than the number of
points in the input data set, and replaces each point in this set by the mean of all points in
the input set that are closer to that point than any other (e.g. within the Voronoi partition of
each updating point). A mean shift algorithm that is similar then to k-means, called likelihood
mean shift, replaces the set of points undergoing replacement by the mean of all points in the

input set that are within a given distance of the changing set. One of the advantages of mean
shift over k-means is that there is no need to choose the number of clusters, because mean
shift is likely to find only a few clusters if indeed only a small number exist. However, mean
shift can be much slower than k-means. Mean shift has soft variants much as k-means does.
6.2 Bilateral filtering
k-means implicitly assumes that the ordering of the input data set does not matter.
The bilateral filter is similar to K-means and mean shift in that it maintains a set of data points
that are iteratively replaced by means. However, the bilateral filter restricts the calculation of
the (kernel weighted) mean to include only points that are close in the ordering of the input
data. This makes it applicable to problems such as image denoising, where the spatial
arrangement of pixels in an image is of critical importance.
6.3 Speaker Matching
During the matching a matching score is computed between extracted feature vectors and
every speaker codebook enrolled in the system. Commonly it is done as a partitioning
extracted feature vectors, using centroids from speaker codebook, and calculating matching
score as a quantization distortion.
Another choice for matching score is mean squared error (MSE), which is computed as the
sum of the squared distances between the vector and nearest centroid divided by number of
vectors extracted from the speech sample.
The quantization distortion (quality of quantization) is usually computed as the sum of
squared distances between vector and its representative (centroid). The well-known distance
measures are Euclidean, city block distance, weighted Euclidean and Mahalanobis. They are
represented in the following equations:

Where x and y are multi-dimensional feature vectors and D is a weighting matrix. When D is
a covariance matrix weighted Euclidean distance also called Mahalanobis distance. Weighted
Euclidean distance where D is a diagonal matrix and consists of diagonal elements of
covariance matrix is more appropriate, in a sense that it provides more accurate identification
result. The reason for such result is that because of their nature not all components in feature
vectors are equally important and weighted distance might give more precise result.

EUCLIDEAN DISTANCE
In mathematics, the Euclidean distance or Euclidean metric is the "ordinary" distance between
two points that one would measure with a ruler, and is given by the Pythagorean formula. By
using this formula as distance, Euclidean space (or even any inner product space) becomes
a metric space. The associated norm is called the Euclidean norm. Older literature refers to the
metric as Pythagorean metric.
The Euclidean distance between points p and q is the length of the line segment connecting
In Cartesian coordinates, if p = (p1, p2,..., pn) and q = (q1, q2,..., qn) are two points
in Euclidean n-space, then the distance from p to q, or from q to p is given by:
The position of a point in a Euclidean n-space is a Euclidean vector. So, p and q are Euclidean
vectors, starting from the origin of the space, and their tips indicate two points. The Euclidean
norm, or Euclidean length, or magnitude of a vector measures the length of the vector:
Where the last equation involves the dot product.
A vector can be described as a directed line segment from the origin of the Euclidean space
(vector tail), to a point in that space (vector tip). If we consider that its length is actually the
distance from its tail to its tip, it becomes clear that the Euclidean norm of a vector is just a
special case of Euclidean distance: the Euclidean distance between its tail and its tip.

The distance between points p and q may have a direction (e.g. from p to q), so it may be
represented by another vector, given by:
In a three-dimensional space (n=3), this is an arrow from p to q, which can be also regarded as
the position of q relative to p. It may be also called a displacement vector if p and q represent
two positions of the same point at two successive instants of time.
The Euclidean distance between p and q is just the Euclidean length of this distance (or
displacement) vector:
Which is equivalent to equation 1, and also to:
7.1One dimension
In one dimension, the distance between two points on the real line is the absolute value of
their numerical difference. Thus if x and y are two points on the real line, then the distance
between them is given by:
In one dimension, there is a single homogeneous, translation-invariant metric (in other words,
a distance that is induced by a norm), up to a scale factor of length, which is the Euclidean
distance. In higher dimensions there are other possible norms.

7.2 Two dimensions
In the Euclidean plane, if p = (p1, p2) and q = (q1, q2) then the distance is given by
This is equivalent to the Pythagorean theorem.
Alternatively, it follows from (2) that if the polar coordinates of the point p are (r1, θ1) and
those of q are (r2, θ2), then the distance between the points is
7.3 Three dimensions
In three-dimensional Euclidean space, the distance is
7.4 N dimensions
In general, for an n-dimensional space, the distance is
7.5 Squared Euclidean Distance
The standard Euclidean distance can be squared in order to place progressively greater weight
on objects that are further apart. In this case, the equation becomes

Squared Euclidean Distance is not a metric as it does not satisfy the triangle inequality,
however it is frequently used in optimization problems in which distances only have to be
It is also referred to as quadrance within the field of rational trigonometry.
7.6 Decision making
The next step after computing of matching scores for every speaker model enrolled in the
system is the process of assigning the exact classification mark for the input speech. This
process depends on the selected matching and modeling algorithms. In template matching,
decision is based on the computed distances, whereas in stochastic matching it is based on the
computed probabilities.
Fig. 7.1 Decision Process
In the recognition phase an unknown speaker, represented by a sequence of feature vectors is
compared with the codebooks in the database. For each codebook a distortion measure is
computed, and the speaker with the lowest distortion is chosen as the most likely speaker.

RESULT AND CONCLUSION
We show the results of our experiments. Every chart is preceded by the short explanation
what we measured and why and followed by the short discussion about results.
8.2 Pruning Basis
First, we start from the basis for speaker pruning. We ran a few tests to see how the matching
function behaves during the identification and when it stabilizes. Chart in Figure 7.1
represents the variation of matching score depending on the available test vectors for 20
different speakers. One vector refers to the one analysis frame.
Fig: 8.1 Distance stabilization
In this figure, the bold line represents the owner of the test sample. It can be seen that at the
beginning the matching score for correct speaker is somewhere among the other scores. But
after large enough amount of new vectors extracted from the test speech, it becomes close
with only few score sand at the end it becomes the smallest score. Actually, this is the

underlying reason for speaker pruning: when we have more data we can drop some of the
models from identification.
8.2.1 Static pruning
In the next experiment, we consider the trade-off between identification error rate and average
time spent on the identification for static pruning. By varying the pruning interval or number
of pruned speakers we expect different error rates and different identification times. From
several runs with different parameter combination we can plot the error rate as a function of
average identification time. To obtain such dependency, we fixed three values for pruning
interval and were varying the number of pruned speakers. The results are shown in Figure 7.3.
Fig: 8.2Evaluation of static variant using different pruning intervals
From this figure we can see that all curves follow almost the same shape. It is because in
order to have fast identification we have to choose either small pruning interval or large
number of pruned speakers. On the other hand, in order to have low error rate we have to
choose large interval or small number of pruned speakers. The main conclusion from this
figure is that these two parameters compensate each other.

8.2.2 Adaptive pruning
The idea of adaptive pruning is based on the assumption that distribution of matching score
follows more or less the Gaussian curve. In Figure 7.4 we can see the distributions of
matching scores for two typical identifications.
Fig: 8.3 Examples of the matching score distribution
From this figure we can see that distribution is not exactly follows the Gaussian curve but its
shape is almost the same. In the next experiment, we consider the trade-off between
identification error rate and average time spenton the identification for adaptive pruning. By
fixing the parameter ŋ and varying the pruning interval we obtained desired dependency.
8.3 Conclusion
The goal of this project was to create a speaker recognition system, and apply it to a speech of
an unknown speaker. By investigating the extracted features of the unknown speech and
then compare them to the stored extracted features for each different speaker in order to
identify the unknown speaker.

The feature extraction is done by using MFCC (Mel Frequency Cepstral Coefficients). The
function „melcepst‟ is used to calculate the melcepstrum of a signal. The speaker was modeled
using Vector Quantization (VQ). A VQ codebook is generated by clustering the training
feature vectors of each speaker and then stored in the speaker database. In this method, the
K means algorithm is used to do the clustering. In the recognition stage, a distortion measure
which based on the minimizing the Euclidean distance was used when matching an unknown
speaker with the speaker database.
During this project, we have found out that the VQ based clustering approach provides
us with the faster speaker identification process.
Project 4380 Report Continuous Deflection Testingctis.utep.edu/reports/Project_4380_Report__Continuous_Deflection_Testing_.pdf · Jitin Arora, B.Tech. Vivek Tandon, Ph.D., PE Soheil
Report B.Tech
B.tech Project Format-2016 Final
B.Tech Dessetation Report
GUIDELINE FOR PREPARATION OF B.Tech SEMINAR/PROJECT REPORTtkmce.ac.in/.../11/Guidelines-Format_for_Seminar_Project_Report-Me… · GUIDELINE FOR PREPARATION OF B.Tech SEMINAR/PROJECT
B.Tech. in Computer Science & Engineeringshiats.edu.in/syllabus/05_BTCSE.pdf · 4 CSIT 699b Project (Project Execution and Report) ... Radiation Balance of Earth and Green House
FADING CHANNEL SIMULATOR - pudn.comread.pudn.com/.../579980/fading_channel_simulator_final_report.pdf · FADING CHANNEL SIMULATOR (B.Tech Project) ... are submitting this report detailing
DITM Project Report Format for B.tech
DIRECTORS MESSAGE - vanguardbschool.com Brochure... · The summer internship project report, ... HUMAN RESOURCES ... PGDM - IIM Bangalore , B.Tech-NITK, Suratkal
B.tech Project Topics
B.Tech Project Presentation
B.Tech Project Report on - National Institute of ...ethesis.nitrkl.ac.in/5703/1/e-77.pdfB.Tech Project Report on Water Quality Analysis of Water Bodies of Kantajhar ... Turbidity also
Numerical Simulation of Collisionless Shockspavanhebbar.github.io › report_BTP.pdfShocks", B.Tech project I report, Department of Aerospace Engineering, Indian Institute of Technology
B.Tech Industrial Training Report
B.Tech final year project
Format for Preparing B.tech Final Year Report
B.Tech Major/ Minor/ LIVE Project with Report, Synopsis and Source Code
GUIDELINES FOR B.TECH PROJECT REPORT PREPARATION · Page | 1 GUIDELINES FOR B.TECH PROJECT REPORT PREPARATION FINAL YEAR PROJECT WORK OBJECTIVES This course will expose students:
mlritm.ac.inmlritm.ac.in/sites/default/files/IV YR PROJECT WORK... · ... IV-B.Tech Work for 2012-16 batch-Reg. Project Work is an important ... with final Project Report, Final Project
B.Tech. Project Report - Indian Institute of Technology …rajam.pdf · B.Tech. Project Report A Reliable Multicast Framework for Applications Raja Mukhopadhyay and Vikas Gupta Department
B.Tech Quality Project 401
Model B.Tech Project Documentation
B.Tech Project
project file for digital image processing for B.tech students
4.b.tech project list 2008 09
My Final Year B.Tech Research Project
B.tech Project Guidelines and Schedule
Department of Civil Engineering B.Tech (Civil Engineering ...gmrit.org/resources/syllabus_5th_6th_civil.pdf · B.Tech (Civil Engineering) COURSE STRUCTURE ... Mini Project/Term paper
Contentssscgj.in/wp-content/uploads/2016/06/SGJ_Q0105_Solar-Proposal... · reviewing of Solar PV project report. ... managing project finance for B.E. / B.Tech. / BBA / B ... these
Project Report B.tech CSE[1]
B.Tech Project 2014-15
10607021 Sarika Tripathi B.tech Project Thesis
GUIDELINE FOR PREPARATION OF SEMINAR REPORTtkmce.ac.in/wp...for_Seminar_Project_ReportMech.pdf · GUIDELINE FOR PREPARATION OF B.Tech SEMINAR/PROJECT REPORT ... Certificate 4. Declaration
Project 2 - B.Tech
12 Example Report Topics (Writing) (PDF)| B2 First (FCE)
- Use an impersonal and semi-formal style.
- The word limit is 140-190 words.
- Spend 40 minutes on the task:
- 5 minutes to plan
- 30 minutes to write
- 5 minutes to check your work
How to write B2 First (FCE) report?
FCE, CAE, CPE
More than practice tests, b2 first (fce) report: writing topics, b2 first (fce) report topic 1.
A group of students from Britain would like to visit your home town as part of an exchange programme. Their leader has asked you to write a report describing what there is to see and do in the town, and to describe some of the other services and facilities that would be available to them.
Write a report.
B2 First (FCE) Report Topic 2
You have just come back from a visit to a local museum organised by your school. The Principal has asked you to write a report about the museum and what you saw there, saying whether it is of interest for all age groups in the school.
B2 First (FCE) Report Topic 3
You have just come back from a two-day study trip to a historic town. Your teacher has asked you to write a report about your visit, saying what you saw during the two days and whether you would recommend a similar visit for other students.
B2 First (FCE) Report Topic 4
A television company is planning to turn the book you have read into a television serial aimed at teenagers.You have been asked to write a report saying whether you think this is a good idea and what changes might be necessary to the plot, the setting or the characters.
B2 First (FCE) Report Topic 5
Your school is planning to start a video club showing films in English. As a member of the committee, you have been asked to write a report suggesting the different types of the film the club should show to appeal to as many students in the school as possible.
B2 First (FCE) Report Topic 6
Your teacher wants to read a short passage from the book you have read to a class of younger students She aims to give them an idea of what the book is like and encourage them to read it. She has asked you to write a report saying which passage from the book would be most suitable and why.
B2 First (FCE) Report Topic 7
The teachers at your school have complained that many students are spending too much time using the Internet to visit social networking sites and chat rooms. They have asked the headteacher to disconnect the Internet from the school’s computer room as they feel it is not an appropriate use of school equipment.
Write a report to the headteacher explaining why internet access should be available to the students. Make some suggestions about ways in which internet access can be controlled.
Get Your (FCE) Report Checked!
B2 first (fce) report topic 8.
You had a class discussion about opportunities for practising English and your teacher has now asked you to write a report for students of English giving them advice.
B2 First (FCE) Report Topic 9
You work for your local tourist information office. Your manager has asked you to write a report on the entertainment facilities in your town. Describe the current facilities and suggest ways in which they could be improved to attract more tourists to the area.
B2 First (FCE) Report Topic 10
A group of British teachers is going to visit your college for two days. The aim of their trip is to learn about how technology is used in education in your country. You have been asked to write a report for the group leader.
Your report should:
- include information about how technology is used to teach different subjects
- recommend which lessons the teachers should watch to see technology being used.
B2 First (FCE) Report Topic 11
Your local government wants to improve your town centre and make it better for local people. Your college principal has asked students to write a report on the situation to send to the local government. In your report you should:
- Describe some of the problems in the town centre
- Suggest, with reasons, what improvements should be made to solve these problems
B2 First (FCE) Report Topic 12
Your English teacher has asked you to write a report on transport facilities in your area.
In your report, you should:
- describe the existing transport facilities
- explain what’s good and bad about them
- suggest how they could be improved in the future.
B2 First (FCE) Report: Writing Topics (PDF)
Download B2 First (FCE) Report: Writing Topics (PDF)
Practice Tests Online
Would you pass b2 first (fce).
- Share full article
Advertisement
Supported by
What the Data Says About Pandemic School Closures, Four Years Later
The more time students spent in remote instruction, the further they fell behind. And, experts say, extended closures did little to stop the spread of Covid.

By Sarah Mervosh , Claire Cain Miller and Francesca Paris
Four years ago this month, schools nationwide began to shut down, igniting one of the most polarizing and partisan debates of the pandemic.
Some schools, often in Republican-led states and rural areas, reopened by fall 2020. Others, typically in large cities and states led by Democrats, would not fully reopen for another year.
A variety of data — about children’s academic outcomes and about the spread of Covid-19 — has accumulated in the time since. Today, there is broad acknowledgment among many public health and education experts that extended school closures did not significantly stop the spread of Covid, while the academic harms for children have been large and long-lasting.
While poverty and other factors also played a role, remote learning was a key driver of academic declines during the pandemic, research shows — a finding that held true across income levels.
Source: Fahle, Kane, Patterson, Reardon, Staiger and Stuart, “ School District and Community Factors Associated With Learning Loss During the COVID-19 Pandemic .” Score changes are measured from 2019 to 2022. In-person means a district offered traditional in-person learning, even if not all students were in-person.
“There’s fairly good consensus that, in general, as a society, we probably kept kids out of school longer than we should have,” said Dr. Sean O’Leary, a pediatric infectious disease specialist who helped write guidance for the American Academy of Pediatrics, which recommended in June 2020 that schools reopen with safety measures in place.
There were no easy decisions at the time. Officials had to weigh the risks of an emerging virus against the academic and mental health consequences of closing schools. And even schools that reopened quickly, by the fall of 2020, have seen lasting effects.
But as experts plan for the next public health emergency, whatever it may be, a growing body of research shows that pandemic school closures came at a steep cost to students.
The longer schools were closed, the more students fell behind.
At the state level, more time spent in remote or hybrid instruction in the 2020-21 school year was associated with larger drops in test scores, according to a New York Times analysis of school closure data and results from the National Assessment of Educational Progress , an authoritative exam administered to a national sample of fourth- and eighth-grade students.
At the school district level, that finding also holds, according to an analysis of test scores from third through eighth grade in thousands of U.S. districts, led by researchers at Stanford and Harvard. In districts where students spent most of the 2020-21 school year learning remotely, they fell more than half a grade behind in math on average, while in districts that spent most of the year in person they lost just over a third of a grade.
( A separate study of nearly 10,000 schools found similar results.)
Such losses can be hard to overcome, without significant interventions. The most recent test scores, from spring 2023, show that students, overall, are not caught up from their pandemic losses , with larger gaps remaining among students that lost the most ground to begin with. Students in districts that were remote or hybrid the longest — at least 90 percent of the 2020-21 school year — still had almost double the ground to make up compared with students in districts that allowed students back for most of the year.
Some time in person was better than no time.
As districts shifted toward in-person learning as the year went on, students that were offered a hybrid schedule (a few hours or days a week in person, with the rest online) did better, on average, than those in places where school was fully remote, but worse than those in places that had school fully in person.
Students in hybrid or remote learning, 2020-21
80% of students
Some schools return online, as Covid-19 cases surge. Vaccinations start for high-priority groups.
Teachers are eligible for the Covid vaccine in more than half of states.
Most districts end the year in-person or hybrid.
Source: Burbio audit of more than 1,200 school districts representing 47 percent of U.S. K-12 enrollment. Note: Learning mode was defined based on the most in-person option available to students.
Income and family background also made a big difference.
A second factor associated with academic declines during the pandemic was a community’s poverty level. Comparing districts with similar remote learning policies, poorer districts had steeper losses.
But in-person learning still mattered: Looking at districts with similar poverty levels, remote learning was associated with greater declines.
A community’s poverty rate and the length of school closures had a “roughly equal” effect on student outcomes, said Sean F. Reardon, a professor of poverty and inequality in education at Stanford, who led a district-level analysis with Thomas J. Kane, an economist at Harvard.
Score changes are measured from 2019 to 2022. Poorest and richest are the top and bottom 20% of districts by percent of students on free/reduced lunch. Mostly in-person and mostly remote are districts that offered traditional in-person learning for more than 90 percent or less than 10 percent of the 2020-21 year.
But the combination — poverty and remote learning — was particularly harmful. For each week spent remote, students in poor districts experienced steeper losses in math than peers in richer districts.
That is notable, because poor districts were also more likely to stay remote for longer .
Some of the country’s largest poor districts are in Democratic-leaning cities that took a more cautious approach to the virus. Poor areas, and Black and Hispanic communities , also suffered higher Covid death rates, making many families and teachers in those districts hesitant to return.
“We wanted to survive,” said Sarah Carpenter, the executive director of Memphis Lift, a parent advocacy group in Memphis, where schools were closed until spring 2021 .
“But I also think, man, looking back, I wish our kids could have gone back to school much quicker,” she added, citing the academic effects.
Other things were also associated with worse student outcomes, including increased anxiety and depression among adults in children’s lives, and the overall restriction of social activity in a community, according to the Stanford and Harvard research .
Even short closures had long-term consequences for children.
While being in school was on average better for academic outcomes, it wasn’t a guarantee. Some districts that opened early, like those in Cherokee County, Ga., a suburb of Atlanta, and Hanover County, Va., lost significant learning and remain behind.
At the same time, many schools are seeing more anxiety and behavioral outbursts among students. And chronic absenteeism from school has surged across demographic groups .
These are signs, experts say, that even short-term closures, and the pandemic more broadly, had lasting effects on the culture of education.
“There was almost, in the Covid era, a sense of, ‘We give up, we’re just trying to keep body and soul together,’ and I think that was corrosive to the higher expectations of schools,” said Margaret Spellings, an education secretary under President George W. Bush who is now chief executive of the Bipartisan Policy Center.
Closing schools did not appear to significantly slow Covid’s spread.
Perhaps the biggest question that hung over school reopenings: Was it safe?
That was largely unknown in the spring of 2020, when schools first shut down. But several experts said that had changed by the fall of 2020, when there were initial signs that children were less likely to become seriously ill, and growing evidence from Europe and parts of the United States that opening schools, with safety measures, did not lead to significantly more transmission.
“Infectious disease leaders have generally agreed that school closures were not an important strategy in stemming the spread of Covid,” said Dr. Jeanne Noble, who directed the Covid response at the U.C.S.F. Parnassus emergency department.
Politically, though, there remains some disagreement about when, exactly, it was safe to reopen school.
Republican governors who pushed to open schools sooner have claimed credit for their approach, while Democrats and teachers’ unions have emphasized their commitment to safety and their investment in helping students recover.
“I do believe it was the right decision,” said Jerry T. Jordan, president of the Philadelphia Federation of Teachers, which resisted returning to school in person over concerns about the availability of vaccines and poor ventilation in school buildings. Philadelphia schools waited to partially reopen until the spring of 2021 , a decision Mr. Jordan believes saved lives.
“It doesn’t matter what is going on in the building and how much people are learning if people are getting the virus and running the potential of dying,” he said.
Pandemic school closures offer lessons for the future.
Though the next health crisis may have different particulars, with different risk calculations, the consequences of closing schools are now well established, experts say.
In the future, infectious disease experts said, they hoped decisions would be guided more by epidemiological data as it emerged, taking into account the trade-offs.
“Could we have used data to better guide our decision making? Yes,” said Dr. Uzma N. Hasan, division chief of pediatric infectious diseases at RWJBarnabas Health in Livingston, N.J. “Fear should not guide our decision making.”
Source: Fahle, Kane, Patterson, Reardon, Staiger and Stuart, “ School District and Community Factors Associated With Learning Loss During the Covid-19 Pandemic. ”
The study used estimates of learning loss from the Stanford Education Data Archive . For closure lengths, the study averaged district-level estimates of time spent in remote and hybrid learning compiled by the Covid-19 School Data Hub (C.S.D.H.) and American Enterprise Institute (A.E.I.) . The A.E.I. data defines remote status by whether there was an in-person or hybrid option, even if some students chose to remain virtual. In the C.S.D.H. data set, districts are defined as remote if “all or most” students were virtual.
An earlier version of this article misstated a job description of Dr. Jeanne Noble. She directed the Covid response at the U.C.S.F. Parnassus emergency department. She did not direct the Covid response for the University of California, San Francisco health system.
How we handle corrections
Sarah Mervosh covers education for The Times, focusing on K-12 schools. More about Sarah Mervosh
Claire Cain Miller writes about gender, families and the future of work for The Upshot. She joined The Times in 2008 and was part of a team that won a Pulitzer Prize in 2018 for public service for reporting on workplace sexual harassment issues. More about Claire Cain Miller
Francesca Paris is a Times reporter working with data and graphics for The Upshot. More about Francesca Paris

IMAGES
VIDEO
COMMENTS
Be sure to back up your points with background information based on research. 2. Gun Control in America. Gun control in the United States is a controversial topic. This type of academic report can either be written as a report that presents both sides of a story or as a persuasive report that argues one side.
100 Innovative Project Topics for BTech Students: Ignite Your Creativity in Engineering. In the world of engineering, innovation is the driving force that propels us forward. As BTech students, you have the unique opportunity to explore your creative potential and make a significant impact on various industries through your projects.
Report writing is both a requirement for completing an engineering qualification at university and a central part of succeeding in future employment. The ability to prepare professional engineering reports is one of the competency standards specified by The Institution of Engineers, Australia (1993) (see Appendix A).
Choosing the right topic is essential for crafting a compelling report. Whether it's for academic, business, or research purposes, an engaging topic will capture the reader's interest and keep them invested in your report. Here are some inspiring report writing topics: 1. The Impact of Technology on Modern Workplaces.
guidelines to the B. Tech students in the preparation of the eighth semester project report. The content of the report, which is submitted to the Institute in partial fulfillment for the award of the degree of Bachelor of Technology, is very much important. It is also imperative that the report, to be acceptable by the Institute,
The aim of this document is to present the basic guidelines on how a report should be constructed for B.Tech project. Any student must confer to the rules and guidelines that have been laid out in the following sections while writing their final report. It must also be kept in mind that the soft copy of the report that any student prepares will ...
English report writing this study advice sheet highlights common features in written reports and makes recommendations for clear presentation and conventional ... B.tech. 999+ Documents. Students shared 9161 documents in this course ... Uploaded by: Anonymous Student. This document has been uploaded by a student, just like you, who decided to ...
A student has to hone these skills and should be adept in these skills, but there are some students who are not aware of the importance of such type of writings. Report writing is one of the most common assignments for students in B.Tech colleges. It is helpful when students need cope with these reports connected with their work.
This is more technical but a required step before you start your project execution. Before you start coding, it is essential to remember that you need to understand what are you going to code ...
13.The report submitted for examination has to be softbound and printed on both sides. The reports should have, on their spines, the abbreviated title of the report, the name of the student, and the year of submission of the report. FORMAT FOR THE REPORT After the text of the report is written, it is to be formatted in an appropriate manner
For each B.Tech. discipline, various project genres/ domains have been kept in mind while curating the B Tech Final Year Projects for you. Computer Science BTech Projects. Several Computer Science-based projects for BTech studentshave been given below by concentrating on several genres like machine and deep learning, Java, Python, Android, etc.
Report Writing Format for Class 10th to 12th. The report writing structure for students in grades 10 and 12 is as follows. Heading : A title that expresses the contents of the report in a descriptive manner. Byline: The name of the person who is responsible for drafting the report. It's usually included in the query.
This document presents the basic guidelines on how a B.Tech project report should be constructed. Every student must follow the rules and guidelines that have been laid out in the following sections while writing their final report. Every student must also submit both soft and hard copy of their project report in the institute library for ...
The report is to be hard bound, cloth covered in the color black. See Exhibit 1. On the spine of the binding the following should be printed or embossed: B.Tech. Project Student's name Year 2.2. Title page. Black & white only on regular paper. See Exhibit 2. 2.3. Certificate. Black & white only from the ECE Department.
Choose from 200+ Topics! Communicating with Colleagues and Peers - Inc. Magazine "Communication experts and CEOs share their strategies for smooth communications with employees, making winning presentations to investors, writing and delivering speeches that get standing ovations, and much more."
Abstract. Our work involves developing a reliable multicast framework that can scale well to both very large networks and very large sessions. The scalability and the efficiency of the framework is estimated by using it as the backbone of 'WhiteBoard', a distributed teleseminaring tool which maintains a shared window supporting graphics and ...
options to format BTech thesis. It also allows one to write a synopsis using the same class file. Also provided is a BIBTEX style file that formats all bibliography entries as per the IIT Tirupati format. The 500 word abstract shall highlight the important features of the thesis/dissertation/report and shall correspond to the electronic version
The report format will be the same across all the education boards in India, and it includes CBSE and ICSE Board as well. Easy to understand examples of report writing have been provided here. All these report writing examples are from the past year's CBSE board exam. Report Writing Class 12 Question 1 (CBSE 2020)
As a third-year student of Computer Science and Engineering (CSE), you must be looking for mini projects to acquire skills and knowledge in… 2 min read · Aug 3, 2023 TechieYan Technologies
A. In class 12, Report Writing is a topic in creative writing skills section. A report can be descriptive or analytical in nature, based on verbal inputs. The question of report writing has to be answered in 120-150 words. There is an internal choice and students have to attempt any one out of the given two options.
200 Seminar Topics for Engineering Students. Welcome to the home of all the latest technical seminar topics. Here engineering students can select the best technical seminar topic ideas on the latest technology. A seminar is a form of academic instruction that may be either at a university or a professional organization.
1. BABU BANARSI DAS INSTITUTE OF TECHNOLOGY, GHAZIABAD. (AFFILIATED TO U.P. TECHNICAL UNIVERSITY, LUCKNOW) (Established in 2000) "REAL TIME SPEAKER RECOGNITION". A project report submitted in partial fulfillment of the requirement for the. Award of Degree of. Bachelor of Technology.
B2 First (FCE) Report: Writing Topics (PDF) A report is usually written for a superior (e.g. a teacher) or a peer group (e.g. members of an English club). You need to give some factual information and make suggestions or recommendations. A report should be clearly organised and include a title and headings. Use an impersonal and semi-formal style.
In districts where students spent most of the 2020-21 school year learning remotely, they fell more than half a grade behind in math on average, while in districts that spent most of the year in ...